AttackIQ Blog
December 19, 2022
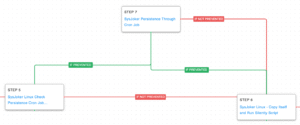
AttackIQ has released a new attack graph that seeks to emulate the activity carried out by the politically motivated Pakistan-based adversary known as APT36 or Transparent Tribe. This newly released attack graph emulates the behaviors observed in attacks against victims working in Indian government organizations.
December 14, 2022
AttackIQ has released a bundle of content including four new attack graphs that seek to emulate two types of attacks conducted by the North Korean adversary BlueNoroff. The newly released graphs emulate the behaviors used in the attacks against the Society for Worldwide Interbank Financial Telecommunication (SWIFT) software and organizations involved in cryptocurrency.
December 13, 2022
OpenAI’s ChatGPT can tell you exactly how to use BAS to improve your cyberdefense effectiveness. But it won’t help you with the Russian military specifically, and that’s a very good thing. See below for why OpenAI deserves credit for this algorithmic limit.
December 12, 2022
We asked OpenAI’s ChaptGPT to write a 750-800 word blog post about breach and attack simulation (BAS) in the voice of Langston Hughes. It did great; see below. And well-done, team OpenAI.
December 8, 2022
A look back at how AttackIQ’s customers and advanced research, as well as key players in the analyst community, helped propel the breach and attack simulation market forward in 2022.
December 3, 2022
AttackIQ has released a new fully featured attack graph that emulates the tactics, techniques, and procedures (TTPs) associated to attacks involving Cuba ransomware.This release is a follow-up to an FBI FLASH alert published in December 2021 that first detailed the initial attacks against 49 entities in critical infrastructure sectors. The Cuba ransomware actors have since doubled the number of U.S. victims and compromised over 100 entities worldwide.
November 18, 2022
AttackIQ has released a new fully featured attack graph that emulates the tactics, techniques, and procedures (TTPs) observed in attacks by cybercriminal groups to deploy their Hive ransomware.
November 17, 2022
AttackIQ has released a new fully featured attack graph that emulates the tactics, techniques, and procedures (TTPs) observed in an attack by Iranian-sponsored adversaries against a Federal Civilian Executive Branch (FCEB) organization in the U.S.
November 3, 2022
What is the correct way to validate your controls against a Text4Shell or similar library vulnerability? You need an adjustable, open systems testing platform to test the specific aspects of your implementation to accurately assess if your security controls are correctly configured to stop attacks that leverage it.
October 31, 2022
One of Ash Carter’s former speechwriters and special assistants reflects on the lessons the Secretary of Defense leaves behind.
October 24, 2022
Most of our development time is focused on the application of risk-based vulnerability management: DeepSurface does the math (there’s a lot of math) and shows you which vulnerabilities carry the greatest risk in your environment, and why. People frequently respond to a demo of DeepSurface with, “That’s amazing… but what do I do next?”
October 6, 2022
AttackIQ has released a new fully featured attack graph that emulates the tactics, techniques, and procedures (TTPs) observed in an attack by Chinese-sponsored adversaries against a Defense Industrial Base organization in the U.S.
September 27, 2022
As we look forward to our next Purple Hats Conference, the industry destination for all cybersecurity professionals, we want to remember and celebrate the winners of our inaugural customer awards program.
September 23, 2022
AttackIQ has released a new fully featured attack graph that emulates the tactics, techniques, and procedures (TTPs) used by Iranian nation-state adversaries against the government of Albania.
September 21, 2022
AttackIQ has released a content bundle including two new attack graphs covering two historical APT28 campaigns involving their SkinnyBoy and Zebrocy malware families and standalone scenarios emulating command-and-control traffic to test boundary controls.
September 16, 2022
AttackIQ has released a new attack graph emulating the techniques used by Iranian actors to compromise and encrypt systems — without the need for malware — to help customers defend against threats that try to operate while living solely off the land.
September 8, 2022
AttackIQ has released a new attack graph emulating a Vice Society attack to help customers validate their security controls and their ability to defend against this threat actor and others who utilize similar behaviors.
August 11, 2022
AttackIQ’s Adversary Research Team has released a new assessment to test endpoint and network controls’ ability to prevent Zeppelin Ransomware.
August 10, 2022
AttackIQ’s Adversary Research Team has released two new assessments to test endpoint and network controls’ ability to prevent widely utilized malware families.
August 4, 2022
The Center for Threat-Informed Defense recently published a methodology and calculator so that you can identify the top MITRE ATT&CK techniques that impact your sector.
August 2, 2022
AttackIQ’s Adversary Research Team has released a new Malware Emulation Attack Graph that emulates the Linux behaviors of the multi-platform backdoor known as SysJoker.
July 29, 2022
In this guest blog post, Bradley Schaufenbuel of Paychex writes about how security teams can leverage the MITRE ATT&CK framework to mount a “threat-informed” defense. This post originally appeared as an article in SC Magazine.
July 29, 2022
Hot off the press, IDC has released an IDC Business value White Paper, sponsored by AttackIQ, that explores the business value and benefits of using the AttackIQ Security Optimization Platform.
July 27, 2022
Organizations today find themselves at a critical turning point in the evolution of their vulnerability management efforts. New vulnerabilities are being published more quickly than teams can credibly analyze and remediate them (currently greater than 75 per day), while at the same time a serious talent shortage has developed. According to CyberSeek, the U.S. cybersecurity workforce has over 950,000 workers, with approximately 465,000 open positions.