On November 17, 2022, the Cybersecurity and Infrastructure Security Agency (CISA) published a joint Cybersecurity Advisory (CSA) with the Federal Bureau of Investigation (FBI) and Health and Human Services (HHS) that continues their #StopRansomware efforts to help organizations protect themselves against Ransomware attacks.
This latest alert concerns the Hive ransomware actors who have compromised over 1,300 victims across the globe and have received over $100 million USD in ransom payments. Hive is a ransomware-as-a-service (RaaS) where a core set of developers work on the malware while affiliates independently conduct the breaches.
Over the last 18 months the Hive ransomware family of affiliates have been observed primarily targeting the Healthcare and Public Health sectors but they also previously compromised other critical infrastructure sectors like Government Facilities, Communications, Critical Manufacturing, and Information Technology.
AttackIQ has released a new fully featured attack graph that emulates a realistic common attack path performed by Hive affiliates. Intelligence from the CSA alert has been correlated with previous open source reporting from vendors at Varonis, Trend Micro, and Microsoft to produce a more detailed attack graph to help customers test their security controls.
Validating your security program performance against AttackIQ’s new attack graph is paramount in reducing risk. By using the AttackIQ Security Optimization Platform, security teams will be able to:
- Evaluate security control performance against an actor who is intent not on just encrypting your files but exfiltrating your data and leaking your secrets.
- Assess their security posture against multiple affiliate actors who operate independently but follow similar attack procedures.
- Continuously validate detection and prevention pipelines against the tactics used by these actors after the variety of initial exploitation opportunities.
Attack Graph: [US-CERT AA22-321A] #StopRansomware: Hive Ransomware
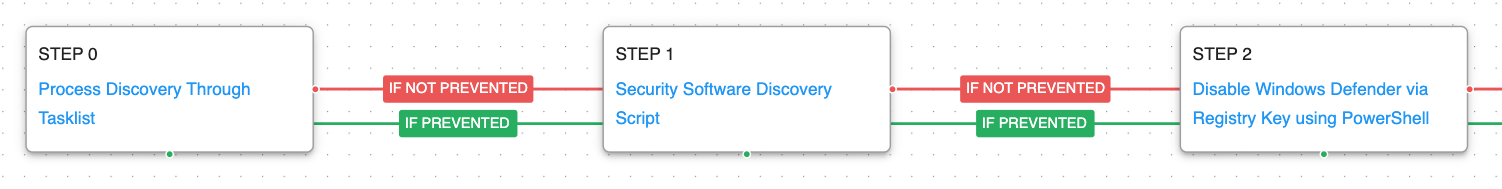
As these attacks are conducted by multiple affiliate actors, the initial infection methods vary wildly between a range of web exploits against all different vendors and web applications to spearphishing with malicious attachments and links. Our attack graph starts after the initial compromise, when the actors first start their hands-on-keyboard activity.
The actors begin by attempting to discover what software is running and more specifically what security software is installed. They want to downgrade the security of the compromised asset by disabling Windows Defender so that their ransomware and additional tools won’t be detected by antivirus.
Process Discovery (T1057): Window’s built-in tasklist command is executed and the results are saved to a file in a temporary location.
Security Software Discovery (T1518.001): A PowerShell script is executed to determine which software has been installed as an AntiVirusProduct class.
Impair Defenses: Disable or Modify Tools (T1562.001): Uses PowerShell to set the DisableAntiSpyware registry key that will prevent Microsoft Defender from running after next reboot.
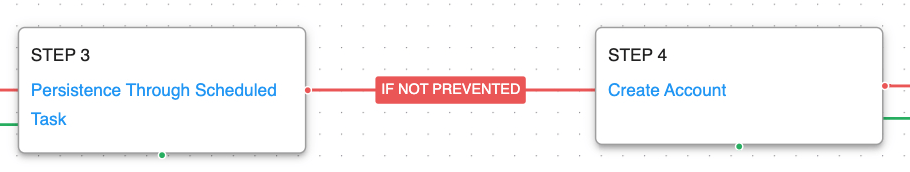
Now that the security of the asset has been degraded, the actor will want to ensure they will continue to have access after reboots. If the actors are currently connected to the host using Cobalt Strike or another shared backdoor they will use scheduled tasks to survive reboots. If they are accessing through a webshell they will try to create an additional account on the system so that it can accessed remotely with Remote Desktop.
Scheduled Task (T1053.005): The Windows Task Scheduler is used to create a task that will execute a command at startup.
Create Account: Local Account (T1136.001): Actors create a new account using net user.
Prior to encryption, the actors will want to locate sensitive data and exfiltrate it to their own infrastructure so that even if you are able to recover the later encrypted data you can be exhorted to pay an additional ransom to not have your data leaked.
File and Directory Discovery (T1083): This scenario uses the native dir command to find files of interest and output to a temporary file.
Exfiltration Over Unencrypted Non-C2 Protocol (T1048.003): This scenario generates fake sensitive data which is exfiltrated over unencrypted HTTP POST requests to an AttackIQ controlled server.
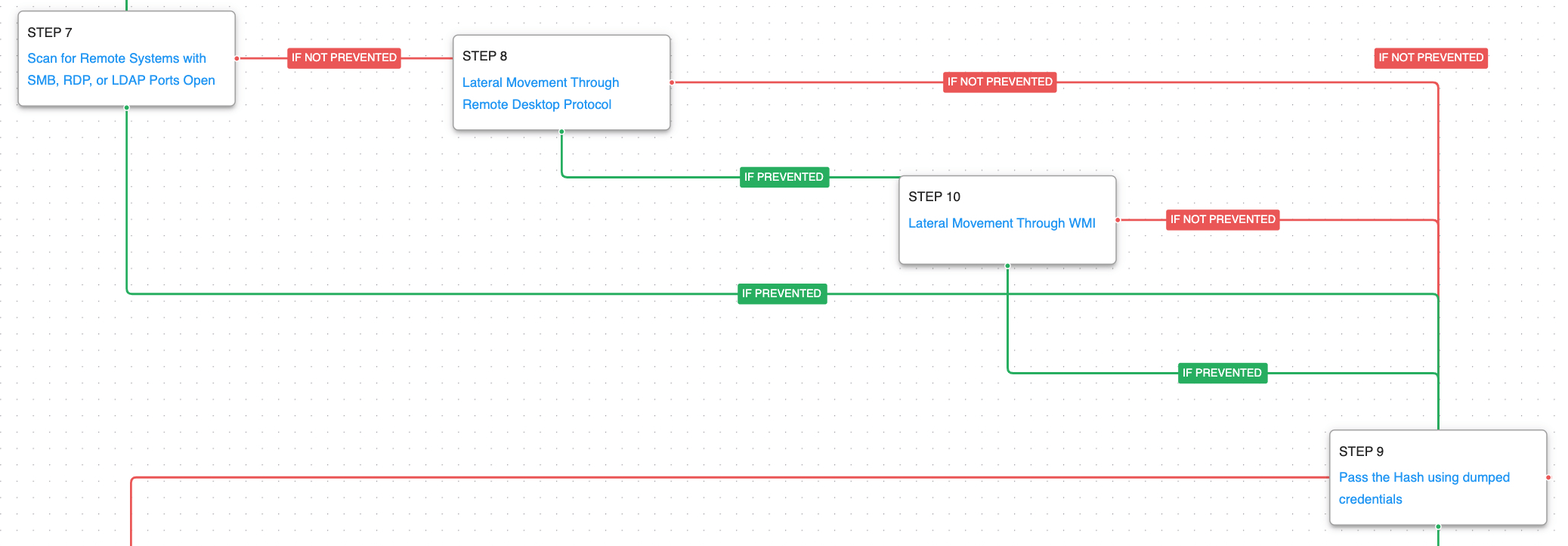
After the data has been harvested from the original point of compromise, the actors will begin to look for other accessible systems so that they can increase the potential impact of their attack. They begin by scanning for any other Windows systems looking for machines with Remote Desktop or File Sharing enabled. They will then attempt to move laterally to those hosts using accounts they initially compromised using either Remote Desktop or WMI. The actors have also been observed using the Pass the Hash technique to gain access to remote systems.
Network Service Discovery (T1046): This scenario uses nmap for scanning hosts that are open on ports 139,389,445,636,3389 that would identify remotely accessible hosts to the attacker.
Remote Services: Remote Desktop Protocol (T1021.001): Remote Desktop is the built-in remote access utility used by Windows. This scenario attempts to remotely connect to another accessible asset with stolen credentials.
Windows Management Instrumentation (T1047): This scenario uses wmic commands to execute commands on a remote target.
Pass the Hash (T1550.002): Using Mimikatz the actors can dump hashes from LSASS memory, and they can be used to authentication via NTLM to other enterprise resources.
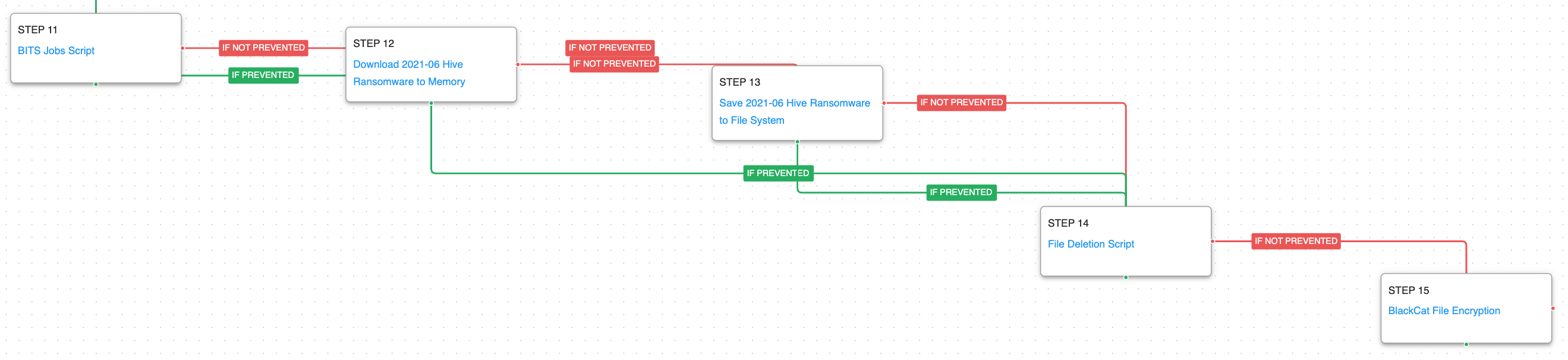
Once all of the data has been collected and the actors have moved as far as they can possibly go, they begin setting the stage to encrypt the files and finish up their ransomware attack. The actor has been observed using BITS jobs to download additional payloads like their Hive ransomware family.
Ingress Tool Transfer (T1105): This scenario downloads to memory and saves to disk in independent scenarios to test network and endpoint controls and their ability to prevent the delivery of known malicious Hive ransomware samples.
BITS Jobs (T1197): Background Intelligent Transfer Service (BITS) is a native mechanism used by legitimate applications to use a system’s idle bandwidth to retrieve files without disrupting other applications. Commands are executed using bitsadmin to create a BITS job and configure it to download a remote payload.
Data Encrypted for Impact (T1486): This scenario performs the file encryption routines used by common ransomware families. Files matching an extension list are identified and encrypted in place using the same encryption algorithms observed in another Rust-based ransomware family.
Detection and Mitigation Opportunities
With so many different techniques being utilized by threat actors, it can be difficult to know which to prioritize for prevention and detection opportunities. AttackIQ recommends first focusing on the following techniques emulated in our scenarios before moving on to the remaining techniques.
1. Scheduled Task/Job: Scheduled Task (T1053.005)
Adversaries may abuse the Windows Task Scheduler to perform task scheduling for initial or recurring execution of malicious code. There are multiple ways to access the Task Scheduler in Windows. The schtasks utility can be run directly from the command line, or the Task Scheduler can be opened through the GUI within the Administrator Tools section of the Control Panel.
1a. Detection
With an EDR or SIEM Platform, you can detect the following commands being issued to schedule a malicious task
Process Name = (“cmd.exe” OR “Powershell.exe”)
Command Line CONTAINS (“schtasks” AND “/CREATE” AND (“cmd” OR “powershell”)
1b. Mitigation
MITRE ATT&CK has the following mitigation recommendations for Scheduled Task/Job: Scheduled Task (T1053.005):
- M1047 – Audit
- M1028 – Operating System Configuration
- M1026 – Privileged Account Management
- M1018 – User Account Management
2. Impair Defenses: Disable or Modify Tools (T1562.001)
Adversaries may modify and/or disable security tools to avoid possible detection of their malware/tools and activities. This may take the many forms, such as killing security software processes or services, modifying / deleting Registry keys or configuration files so that tools do not operate properly, or other methods to interfere with security tools scanning or reporting information
2a. Detection
Using an EDR or SIEM product, you can detect when Microsoft Defender Registry Key’s Value for “DisableAntiSpyware” has been set to 1, disabling the security control:
Process Name = “reg.exe”
Command Line CONTAINS (“HKLM\SOFTWARE\Policies\Microsoft\Windows Defender”
AND “DisableAntiSpyware” AND “REG_DWORD /d 1”)
2b. Mitigation
MITRE ATT&CK Recommends the following mitigations for Impair Defenses: Disable or Modify Tools (T1562.001):
- M1022 – Restrict File and Directory Permissions
- M1024 – Restrict Registry Permissions
- M1018 – User Account Management
3. Create Account: Local Account (T1136.001)
Post compromise, this threat actor has been observed creating accounts on the compromised local machines so they can upgrade shell access to full GUI RDP access.
3a. Detection
With an EDR or SIEM product, you can utilize custom queries and detections to alert when non authorized/ unexpected users attempt to create a user account on the local machine. Although this is a benign windows feature, visibility of users utilizing this feature could lead to earlier detections of malicious entities in your environment.
Process Name = (“cmd.exe” OR “Powershell.exe”)
Command Line CONTAINS (“net user” AND “/add”)
3b. Mitigation
MITRE ATT&CK Recommends the following mitigations for Create Account: Local Account (T1136.001):
Wrap-up
In summary, this attack graph will evaluate security and incident response processes and support the improvement of your security control posture against multiple affiliate actors who operate independently but in similar manners. With data generated from continuous testing and use of this attack graph, you can focus your teams on achieving key security outcomes, adjust your security controls, and work to elevate your total security program effectiveness against a known and dangerous threat.
AttackIQ stands at the ready to help security teams implement this attack graph and other aspects of the AttackIQ Security Optimization Platform, including through our co-managed security service, AttackIQ Vanguard.