On November 16, 2022, the Cybersecurity and Infrastructure Security Agency (CISA) published a joint Cybersecurity Advisory (CSA) with the Federal Bureau of Investigation (FBI) that details suspected Iranian government-sponsored actors’ tactics, techniques, and procedures (TTPs) used in a cyber-attack to install a Crypto Miner.
In April 2022, CISA identified malicious activity between a FCEB organization and a known malicious IP address associated with the exploitation of the Log4Shell vulnerability (CVE-2021-44228) in VMware Horizon servers. From mid-June through mid-July 2022, CISA conducted an incident response engagement and determined that the organization was compromised as early as February 2022.
After successful exploitation of the Log4Shell vulnerability, the threat actors weakened the victim’s security controls, installed the XMRig crypto mining malware, and moved laterally to the domain controller. From there they compromised credentials with the use of Mimikatz and installed Ngrok reverse proxies to allow for the tunneling of Remote Desktop connections.
Validating your security program performance against AttackIQ’s new attack graph is paramount in reducing risk. By using the AttackIQ Security Optimization Platform, security teams will be able to:
- Evaluate security control performance against common PowerShell techniques that allow for delivery of malware.
- Assess their security posture against a threat actor who is able to downgrade the security controls in your environment.
- Continuously validate detection and prevention pipelines beyond the multitude of initial access exploits used by actors.
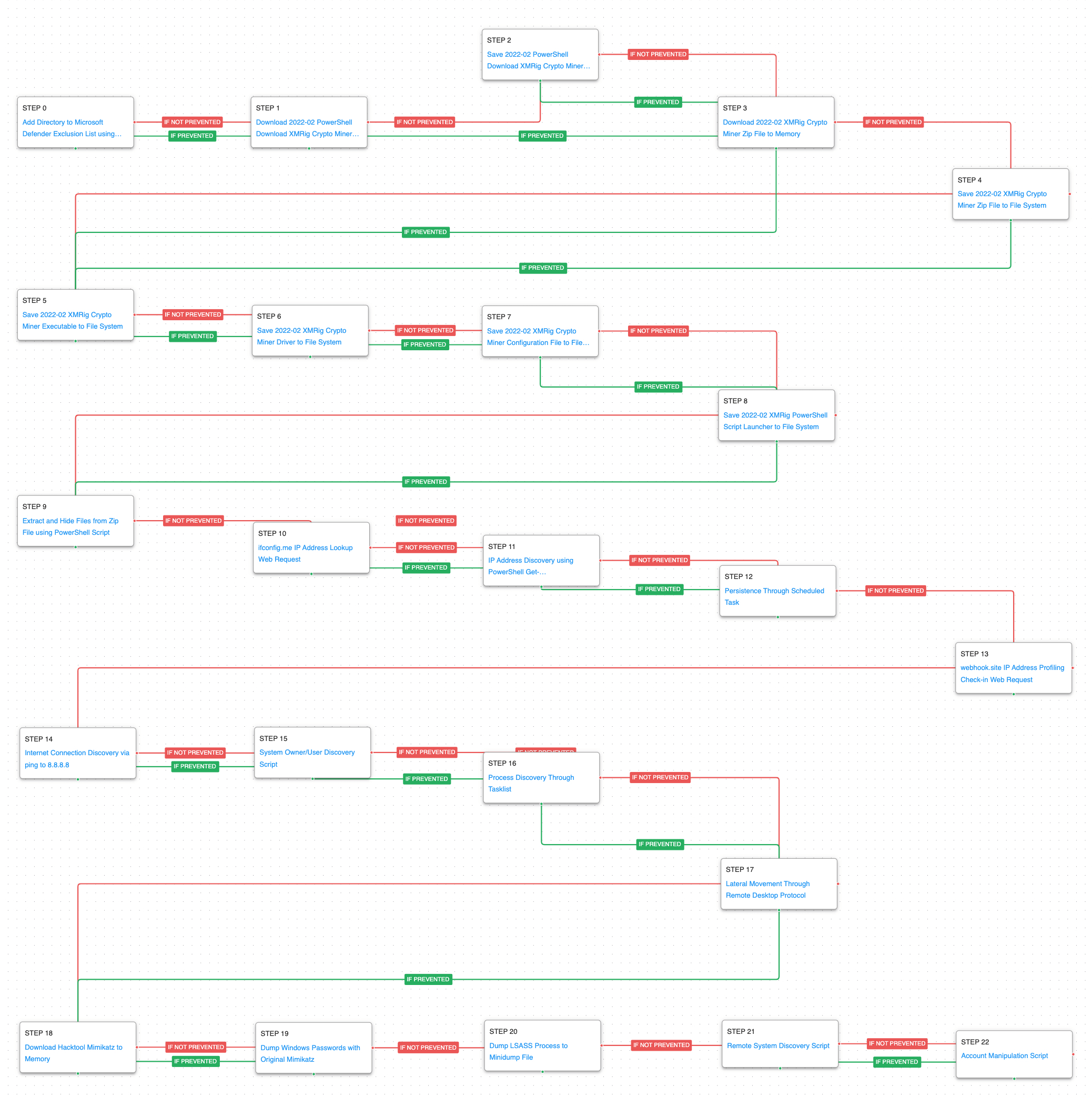
Attack Graph: [US-CERT AA22-320A] Iranian Government-Sponsored APT Actor Deploys Crypto Miner
Our attack graph begins after the initial exploitation of the Log4Shell vulnerability and starts with the execution of a PowerShell command that adds the C:\ drive to the exclusion list of Windows Defender. Immediately afterwards, the adversary starts a cascade of downloads to obtain all the files needed to carry out the attack. This graph contains additional techniques not covered in the US-CERT alert taken from our own internal research into the malware and PowerShell scripts used in this attack. This intent of this attack graph is to emulate the actor’s true behaviors instead of just similar general techniques.
Impair Defenses: Disable or Modify Tools (T1562.001): As part of the PowerShell commands executed by the threat actor, they use the Add-MpPreference cmdlet to add the entire C:\ drive to the exclusion list in Microsoft Defender.
Ingress Tool Transfer (T1105): The cascade of scenarios downloads to memory and saves to disk in two separate scenarios an array of files to test network and endpoint controls and their ability to prevent the delivery of known malicious content. The actors and these scenarios use PowerShell to download the second stage of their attack.
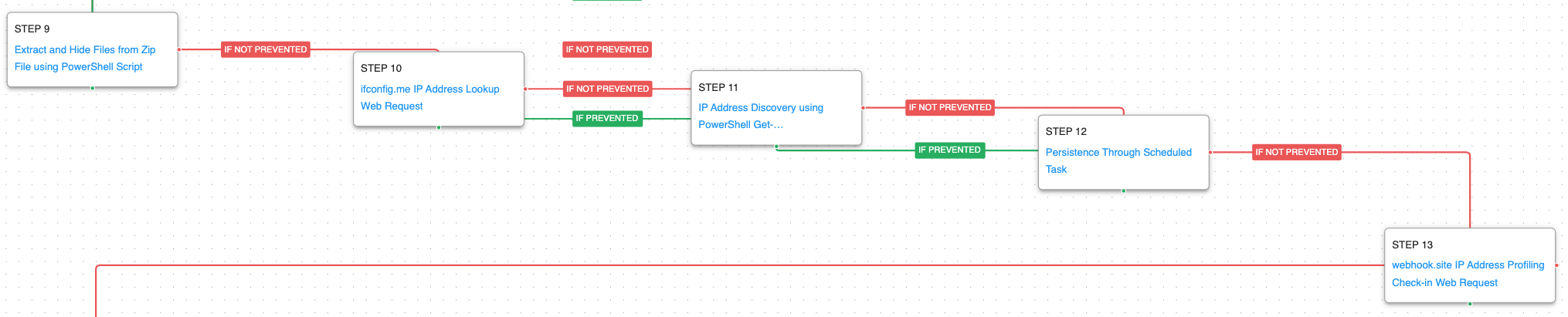
After successfully downloading the next stages, the adversary extracts the XMRig crypto miner payloads from a zip file and collects external and internal information about the network adapters. A scheduled task is created to persistently execute the crypto mining malware before finally sending a request to a 3rd party website to track infection status.
Hide Artifacts: Hidden Files and Directories (T1564.001): The PowerShell code will extract the files to an inconspicuous directory and the iterates through each file and sets the Hidden attribute to True. Setting this attribute not only attempts to hide the files from defenders but makes their accidental deletion more difficult.
System Network Configuration Discovery (T1016): The actor will attempt to retrieve both the external and internal IP address of infected host. The external data is collected by making an HTTP GET request to the legitimate service ifconfig.me while the internal IP address is collected using a native PowerShell cmdlet.
Scheduled Task/Job: Scheduled Task (T1053.005): One of the executables dropped from the zip file is a binary that will configure and start executing the XMRig crypto miner. A Scheduled Task named RuntimeBrokerService is created and set to run daily as SYSTEM to ensure that the machine will continue to mine currency after a reboot.
Web Service: One-Way Communication (T1102.003): After the scheduled task has successfully been created the actor makes an HTTP POST request to the 3rd party service webhook.site. This service creates a unique canary token URL that when accessed records details about the request including the source IP address. Results are recorded in an interface accessible to the original user and the site can even send email alerts when new requests are received. The threat actors use this site to track their infections.
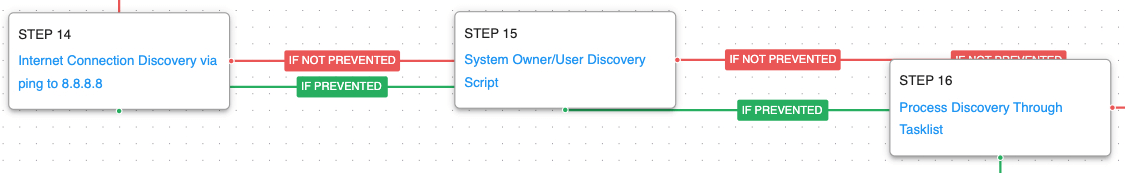
When the scheduled task is executed, the binary will decode additional PowerShell code and execute it in a new PowerShell process. The new malware stage first validates there is network connectivity by pinging Google’s DNS servers and then executes a query user command to collect the running user’s name. The running processes are collected and checked to see if the Task Manager or Process Hacker is running before starting the crypto mining activity. The actor is doing this to prevent executing if a defender may be analyzing the system during runtime.
Internet Connection Discovery (T1016.001): The actors used ping to Google’s 8.8.8.8 DNS server to verify if they could connect to the internet.
System Owner/User Discovery (T1033): query user and whoami are called to determine what account the malware is currently operating under.
Process Discovery (T1057): Window’s built-in tasklist command is executed as a command process and the results are saved to a file in a temporary location.
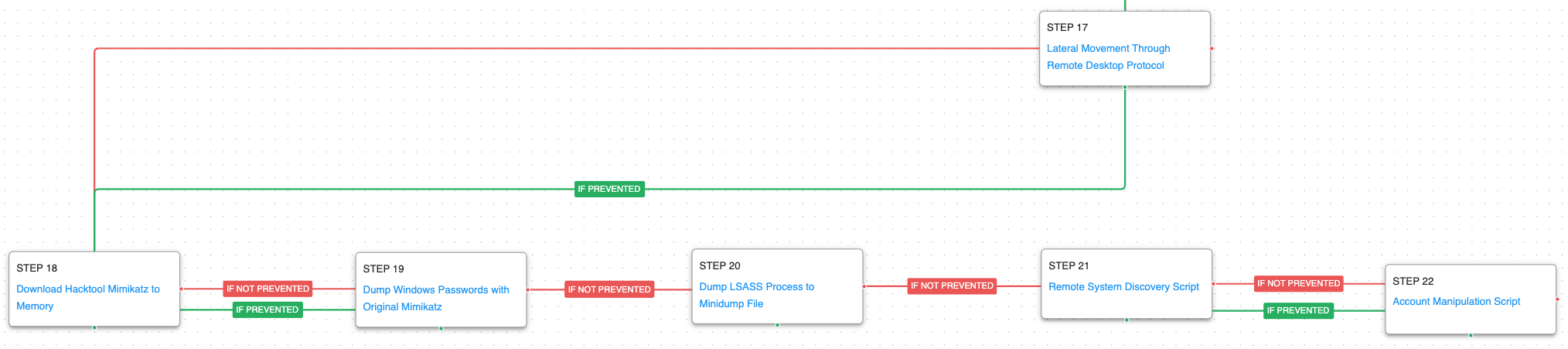
After succeeding at executing their crypto miner malware, the actor begins to move around laterally. The use Remote Desktop to move to another host in the local network, download Mimikatz from a file sharing service, and begin to dump additional credentials. They continue to discover more about the internal network and make modifications to local accounts to help ensure their persistence.
Remote Desktop Protocol (T1021.001): The adversary leveraged RDP to propagate to several hosts within the network.
Credentials from Password Stores: Windows Credential Manager (T1555.004): Mimikatz is used to dump additional credentials that would aid the actor in moving to additional hosts.
OS Credential Dumping: LSASS Memory (T1003.001): The adversary was observed trying to dump LSASS process through the use of the Task Manager. This process contains additional credentials and secrets that can also help the actor move laterally to additional hosts and add more machines to the crypto mining botnet.
Remote System Discovery (T1018): This scenario executes the net view command to gather additional hosts available to the infected asset.
Account Manipulation (T1098): The actors would create and enable additional accounts to enable persistence from multiple users. This scenario enables the local guest account.
Opportunities for Extending the Attack Graph
There are additional scenarios that can be added to the attack graph to test additional security controls related to the attack.
Log4Shell (CVE-2021-44228) Signature-Based Web Request – VMWare Horizon: We have released a handful of different scenarios that can send the HTTP payloads that are required to exploit the various Log4Shell vulnerabilities. We’ve published a series of blogs with guidance on how to best test these vulnerabilities. These scenarios need to be configured to point to an external server that maybe vulnerable and customized to ensure the write URI paths are tested.
Cryptocurrency Mining: This scenario consumes CPU cycles by performing cryptographic operations like the ones used in cryptocurrency mining operations. This scenario was not originally added to the attack graph by default as it will use up the cycles on the running asset. Customers can selectively add this step to the graph for hosts where slowdowns are more acceptable.
Lateral Movement Through PAExec: The threat actors also download PsExec to move laterally and execute commands on remote systems using a user’s credentials. This scenario can be added and configured with additional credentials to emulate that behavior as an additional lateral movement technique.
Detection and Mitigation Opportunities
With so many different techniques being utilized by threat actors, it can be difficult to know which to prioritize for prevention and detection opportunities. AttackIQ recommends first focusing on the following techniques emulated in our scenarios before moving on to the remaining techniques.
- Impair Defenses: Disable or Modify Tools (T1562.001)
Adversaries may modify and/or disable security tools to avoid possible detection of their malware/tools and activities. This may take many forms, such as killing security software processes or services, modifying / deleting Registry keys or configuration files so that tools do not operate properly, or other methods to interfere with security tools scanning or reporting information. Adversaries may also disable updates to prevent the latest security patches from reaching tools on victim systems.
1a. Detection
With an EDR or SIEM Platform, you can detect the following commands being issued to exclude the C:\ drive from Microsoft Defender scanning:
Process Name == Powershell.exe
Command Line CONTAINS (“Add-MpPreference” AND “-ExclusionPath”)
1b. Mitigation
- MITRE ATT&CK has the following mitigation recommendations for Impair Defenses: Disable or Modify Tools (T1555.001):
- Scheduled Task/Job: Scheduled Task (T1053.005)
Adversaries may abuse the Windows Task Scheduler to perform task scheduling for initial or recurring execution of malicious code. There are multiple ways to access the Task Scheduler in Windows. The schtasks utility can be run directly on the command line, or the Task Scheduler can be opened through the GUI within the Administrator Tools section of the Control Panel.
2a. Detection
With an EDR or SIEM Platform, you can detect the following commands being issued to schedule a malicious task named “RuntimeBrokerService”
Process Name = (“cmd.exe” OR “Powershell.exe”)
Command Line CONTAINS (“schtasks” AND “/CREATE” AND “RuntimeBrokerService” AND (“cmd” OR “powershell”)
2b. Mitigation
- MITRE ATT&CK has the following mitigation recommendations for Scheduled Task/Job: Scheduled Task (T1053.005):
- Credentials from Password Stores: Windows Credential Manager (T1555.004):
Adversaries may acquire credentials from the Windows Credential Manager. The Credential Manager stores credentials for signing into websites, applications, and/or devices that request authentication through NTLM or Kerberos in Credential Lockers (previously known as Windows Vaults).
3a. Detection
With an EDR or SIEM Platform, you can detect the following commands being issued to run Mimikatz.exe on an endpoint:
Process Name == (“cmd.exe” OR “Powershell.exe”)
Command Line CONTAINS (“sekurlsa::logonpasswords”)
3b. Mitigation
- MITRE ATT&CK has the following mitigation recommendations for Credentials from Password Stores: Windows Credential Manager (T1555.004):
Wrap-up
In summary, this attack graph will evaluate security and incident response processes and support the improvement of your security control posture against an actor who uses both native system tools and their own bespoke PowerShell scripts. With data generated from continuous testing and use of this attack graph, you can focus your teams on achieving key security outcomes, adjust your security controls, and work to elevate your total security program effectiveness against a known and dangerous threat.
AttackIQ stands at the ready to help security teams implement this attack graph and other aspects of the AttackIQ Security Optimization Platform, including through our co-managed security service, AttackIQ Vanguard.