Product & Platform
January 17, 2024
GootLoader, a stealthy JavaScript-based downloader, has posed a persistent threat to Windows-based systems since 2020. In this article, we’ll delve into who Gootloader is and how organizations can effectively emulate and test against this threat using AttackIQ Flex, a powerful agentless breach and attack simulation tool. The exciting part? You can sign up for AttackIQ Flex for free, providing you with an opportunity to outsmart this digital menace.
January 10, 2024
AttackIQs Engineering Team recently took another innovative step forward in cybersecurity, mapping our content to Sigma Rules and deploying a library to convert rules to product queries to improve detection efficacy through enhanced mitigation recommendations. Dubbed SigmAIQ, this is the first opensource repository of its kind, and yet another tool AttackIQ has added to our already vast testing and detection arsenal.
January 4, 2024
As 2023 draws to a close, AttackIQ is proud to present a comprehensive recap of a transformative year marked by groundbreaking achievements and advancements in the realm of cybersecurity. This year has seen us reach new heights in innovation, collaboration, and commitment to fortifying global defenses against evolving cyber threats.
December 27, 2023
We’ve got you covered this holiday season. AttackIQ Flex now includes adversary emulation for Nobelium’s cyber threats to TeamCity servers.
December 20, 2023
As we’ve seen time and time again in our cybersecurity landscape, the wicked prey on the weary and take no prisoners along the way. Rhysida, an emerging ransomware group, serves as a perfect example of this. While their activities span across a variety of sectors and regions around the world, they have taken a keen taste to vulnerabilities found within the realm of healthcare.
December 12, 2023
The National Security Agency (NSA) and Cybersecurity and Infrastructure Security Agency (CISA) recently released their top 10 list of common cybersecurity misconfigurations. Some of these include your standard slew of don’t use default software settings, don’t make weak passwords, and don’t practice poor MFA hygiene. No surprise there for most security teams, but apparently, it’s common enough that they all made the top 10 list of things people do anyway.
November 20, 2023
Though the band Soft Cell may be considered a one-hit wonder with their 1981 hit song “Tainted Love”, the same cannot be said for Gallium, a Chinese-based threat actor that has continued to wreak havoc in the Middle Eastern telecommunications sector for over a decade now. Their most recent cyberespionage campaign? Operation Tainted Love.
November 7, 2023
We just made agentless, automated security control testing even easier, cheaper, and more powerful than ever before. Now there’s no excuse not to find those security gaps you’re missing.
November 2, 2023
In the covert realm of cyberspace, a formidable adversary has emerged – a state-sponsored, North Korean group known as Kimsuky. Their clandestine operations are not motivated by profit, but by the pursuit of state secrets and strategic intelligence for the Democratic People’s Republic of Korea (DPKR).
October 26, 2023
If you’ve at all followed the work of AttackIQ’s Adversary Research Team (ART) in recent years, you’re well aware of their relentless pursuit for actionable, incisive, quantitative, and cutting-edge insights into the art (no pun intended) of adversary emulation.
October 18, 2023
As newer and more sophisticated threats continue to enter today’s cyber landscape, content filtering remains a tried-and-true tool that aids organizations in threat prevention, regulatory compliance, network security and policy enforcement by controlling and managing the type of content users can access or share based on defined criteria. Making sure these policies work is critical in preventing insider threats and maintaining compliance with corporate usage policies.
October 11, 2023
In the ongoing battle against cyber threats, the synergy between Endpoint Antivirus (AV) software and a cutting-edge solution like AttackIQ Flex plays a pivotal role in fortifying your defenses.
October 4, 2023
EDR testing is a critical component of maintaining a bulletproof defense posture, but it doesn’t have to be hard to do.
September 27, 2023
AttackIQ has released a new Flex package designed to replicate the activities associated with the recent supply chain attack on 3CX software by Lazarus Group, a North Korean-based adversary.
September 19, 2023
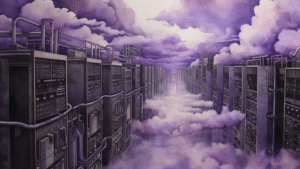
Programmatic cloud testing can be your true north.
September 7, 2023
The rise of remote work, branch networks, and the entwining of IoT and OT systems have created vast network footprints, making identifying vulnerabilities more challenging than ever. Cyber threats loom large, and with the stakes higher than ever, ensuring your defenses are impervious is paramount.
August 31, 2023
In a world where time is a precious resource, AttackIQ Flex ensures your security controls are prepared for the challenges posed by M&A and remote network integrations.
August 23, 2023
The implications of not conducting security control testing are profound. Adversaries are relentless and will exploit vulnerabilities if given the chance. The potential impact includes data breaches, financial losses, damage to reputation, and regulatory penalties.
August 3, 2023
AttackIQ has helped hundreds of companies across the global 2000 to conduct automated testing at scale, powered by MITRE ATT&CK. Building on a decade of success, we are now making testing available for everyone. Here’s what that means.
March 17, 2023
AttackIQ has released a new attack graph that emulates the Tactics, Techniques, and Procedures (TTPs) used by a cybercriminal-focused adversary who carried successfully exploited CVE-2019-18935 against an instance of Telerik UI at a federal civilian executive branch (FCEB) agency.
September 27, 2022
As we look forward to our next Purple Hats Conference, the industry destination for all cybersecurity professionals, we want to remember and celebrate the winners of our inaugural customer awards program.