On May 11, 2023, the Cybersecurity and Infrastructure Security Agency (CISA) released a joint Cybersecurity Advisory (CSA) detailing ongoing exploitation of a vulnerability in PaperCut MF and NG by cyber criminals. CVE-2023-27350 is a critical vulnerability that allows for remote, unauthenticated attacks to bypass authentication and execute arbitrary code as the System user account. PaperCut released a patch for their enterprise printing management software in March 2023, but many users have yet to patch their externally facing services which are now being targeted with ransomware.
The vulnerability is trivial to exploit and takes advantage of Session Puzzling where any user can access the webpage directly that appears after setup is initially completed. Once there, a Login button is available that will automatically log the user into the system with administrative privileges.
After being logged in, an attacker can enable the functionality to run user-provided Java code on the print management server.
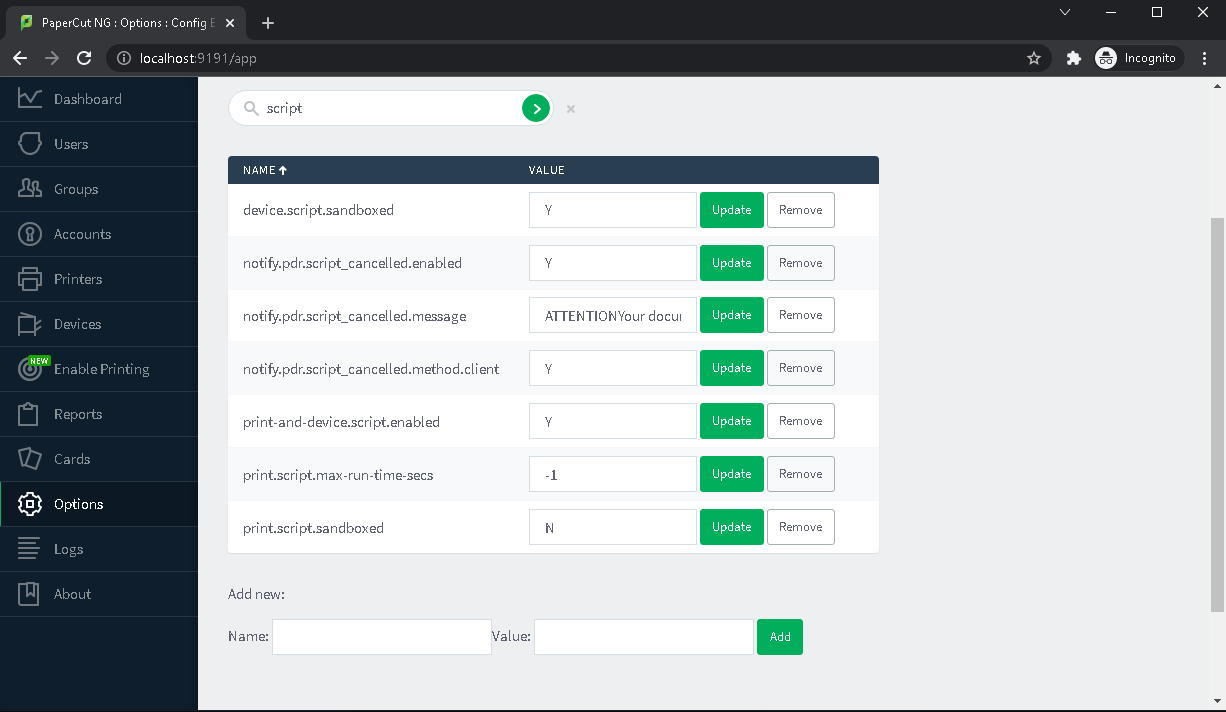
The actor can then access the print server configuration page and access the scripting tab. Malicious Java code and be added and executed to establish a remote shell or force the print server to download and execute additional remote payloads.
AttackIQ has released four new scenarios that emulates the exploitation of CVE-2023-27350 to help customers validate their security controls and their ability to defend against this widely exploited vulnerability.
PaperCut MF/NG SetupCompleted Authentication Bypass Web Request (CVE-2023-27350)
This scenario is configured to send a specially crafted web request to a PaperCut server that is associated with the completed setup page. The data returned by the web server is evaluated to see if the page with the login button is returned to the user that would validate if the server were still vulnerable to the authentication bypass method.
PCAP Replay – PaperCut MF/NG SetupCompleted Authentication Bypass (CVE-2023-27350) & PCAP Replay – PaperCut MF/NG Remote Code Execution (CVE-2023-27350)
These two scenarios use AttackIQ’s Boundary Posture Management (BPM) to replay network traffic between two hosts across a network security control to test the ability for security controls to block and prevent malicious network traffic.
The first PCAP contains traffic that replays the access of the SetupCompleted page and the logging into the portal with administrative controls. The second PCAP includes the injection of malicious Java code into the scripting portal and executing remote commands on the print server.
Critical Vulnerabilities in PaperCut Print Management Software
This scenario attempts to make connection requests to the malicious infrastructure referenced in the CISA advisory. This is designed to test DNS sinkhole and proxy blocking capabilities to known malicious infrastructure.
Additional Emulation Options
The CISA advisory identifies one of the actors abusing this vulnerability as the Bl00dy Ransomware Gang. This actor has previously been identified using LockBit 3.0 as part of its ransomware attacks. AttackIQ released a fully featured attack graph that emulates LockBit 3.0’s capabilities in March 2023.
Detection and Mitigation Opportunities
As with all critical vulnerabilities, the primary mitigation is having a robust patching and management program. This vulnerability was discovered, reported, and patch in March 2023 and two months later vulnerable, unpatched servers continue to be targeted by multiple actors at scale.
Patching critical externally facing vulnerabilities is critical to keeping your networks secure.
If patching is not possible, CISA has identified two rules from Emerging Threats that can be used to detect attempts that begin the initial exploitation of the vulnerability.
alert http any any -> $HOME_NET any (msg:"ET EXPLOIT PaperCut MF/NG SetupCompleted Authentication Bypass (CVE-2023-27350)"; flow:established,to_server; http.method; content:"GET"; http.uri; content:"/app?service=page/SetupCompleted"; bsize:32; fast_pattern; reference:cve,2023-27350; classtype:attempted-admin;)
alert http any any -> $HOME_NET any (msg:"ET EXPLOIT PaperCut MF/NG SetupCompleted Authentication Bypass (CVE-2023-27350)"; flow:established,to_server; http.method; content:"GET"; http.uri; content:"page/SetupCompleted"; fast_pattern; reference:url,www.huntress.com/blog/critical-vulnerabilities-in-papercut-print-management-software; reference:cve,2023-27350; classtype:attempted-admin; metadata:attack_target Server, cve CVE_2023_27350, deployment Perimeter, deployment Internal, deployment SSLDecrypt, former_category EXPLOIT, performance_impact Low, confidence High, signature_severity Major, updated_at 2023_05_05;)
The web request and PCAP replay scenarios will trigger these two rules along with other vendor security controls that are looking for exploitation of CVE-2023-27350.
Wrap-up
In summary, these new scenarios will help evaluate security and incident response processes and support the improvement of your security control posture against the PaperCut vulnerability.
AttackIQ stands at the ready to help security teams implement this attack graph and other aspects of the AttackIQ Security Optimization Platform, including through our fully managed service, AttackIQ Ready!, and our co-managed security service, AttackIQ Vanguard.