Threat Advisories
November 18, 2022
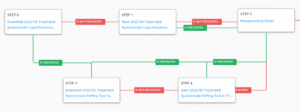
AttackIQ has released a new fully featured attack graph that emulates the tactics, techniques, and procedures (TTPs) observed in attacks by cybercriminal groups to deploy their Hive ransomware.
November 17, 2022
AttackIQ has released a new fully featured attack graph that emulates the tactics, techniques, and procedures (TTPs) observed in an attack by Iranian-sponsored adversaries against a Federal Civilian Executive Branch (FCEB) organization in the U.S.
October 6, 2022
AttackIQ has released a new fully featured attack graph that emulates the tactics, techniques, and procedures (TTPs) observed in an attack by Chinese-sponsored adversaries against a Defense Industrial Base organization in the U.S.
September 23, 2022
AttackIQ has released a new fully featured attack graph that emulates the tactics, techniques, and procedures (TTPs) used by Iranian nation-state adversaries against the government of Albania.
September 16, 2022
AttackIQ has released a new attack graph emulating the techniques used by Iranian actors to compromise and encrypt systems — without the need for malware — to help customers defend against threats that try to operate while living solely off the land.
September 8, 2022
AttackIQ has released a new attack graph emulating a Vice Society attack to help customers validate their security controls and their ability to defend against this threat actor and others who utilize similar behaviors.
August 11, 2022
AttackIQ’s Adversary Research Team has released a new assessment to test endpoint and network controls’ ability to prevent Zeppelin Ransomware.
August 10, 2022
AttackIQ’s Adversary Research Team has released two new assessments to test endpoint and network controls’ ability to prevent widely utilized malware families.
June 28, 2022
AttackIQ has released two new fully featured attack graphs emulating the tactics, techniques, and procedures (TTPs) used by likely nation-state adversaries that continue exploiting the Log4Shell vulnerability in VMware Horizon Systems.
June 24, 2022
In response to US-CERT Alert AA22-174A, AttackIQ has released new malware transfer scenarios to the platform and recommends validating security controls using previously released scenarios addressing Log4Shell and the VMware CVE-2022-22954 vulnerability.
June 3, 2022
AttackIQ has released a new fully featured attack graph emulating the tactics, techniques, and procedures used by the Karakurt Data Extortion Group recently reported in US-CERT Alert AA22-152.
June 2, 2022
AttackIQ has released a new scenario and assessment in response to US-CERT Alert AA22-152A, Karakurt Data Extortion Group
April 29, 2022
Uncover new attacks from a threat actor likely operating out of Belarus known as UNC1151 or Ghostwriter.
April 1, 2022
AttackIQ has released a new attack graph for organizations to test and validate their cyberdefense effectiveness against the HAVEX strain of malware. This attack graph follows a pair of Department of Justice indictments of Russia-based threat actors and a new joint FBI-CISA Cybersecurity Advisory about HAVEX released last week. An enduring and dangerous threat, HAVEX targeted the energy and power sectors in 135 countries from 2012-2018, and the tactics and techniques within it continue to threaten organizations today.
March 18, 2022
AttackIQ has released a new attack graph to emulate Russia-based threat actors as they exploit multi-factor authentication protocols to disable MFA. This blog describes the scenarios we have included in the new attack graph to emulate the adversary and then, to inform a purple team construct for cyberdefense operations, it provides detection and mitigation recommendations that you can use to improve your security program effectiveness. Read on for more.
February 24, 2022
In anticipation of escalating cyberattacks by the Russian government against U.S. and allied interests, AttackIQ has developed a new attack graph to help organizations test and validate their cyberdefenses against known Russian adversarial tactics, techniques, and procedures (TTPs).