Mustang Panda is a state-sponsored and politically motivated Chinese adversary that has been active since at least 2012. This actor, also known as Bronze President, TA416, HoneyMyte, and TEMP.Hex, is closely aligned with Chinese interests, demonstrating a particular focus on organizations located in the United States and Southeast Asia.
One of the primary tools used by this adversary is a shared piece of Chinese malware known as PlugX. This piece of malware has been used by multiple Chinese actors since 2008 and is a remote access Trojan (RAT) commonly used to establish a persistent backdoor, conduct environmental reconnaissance efforts, exfiltrate sensitive data, and executing additional payloads. Additionally, recent attacks have used a new bespoke malware family called TONESHELL as the actor’s primary payload believed to be exclusive to Mustang Panda.
AttackIQ has released two new attack graphs that seek to emulate Mustang Panda with the objective of helping customers validate their security controls and their ability to defend against this threat. Validating your security program performance against these behaviors is vital in reducing risk. By using these new attack graphs in the AttackIQ Security Optimization Platform, security teams will be able to:
- Evaluate security control performance against recently active Chinese APT activity.
- Assess their security posture against an actor who globally targets Government and Defense organizations.
- Continuously validate detection and prevention pipelines against other Chinese actors who also leverage PlugX in the attacks.
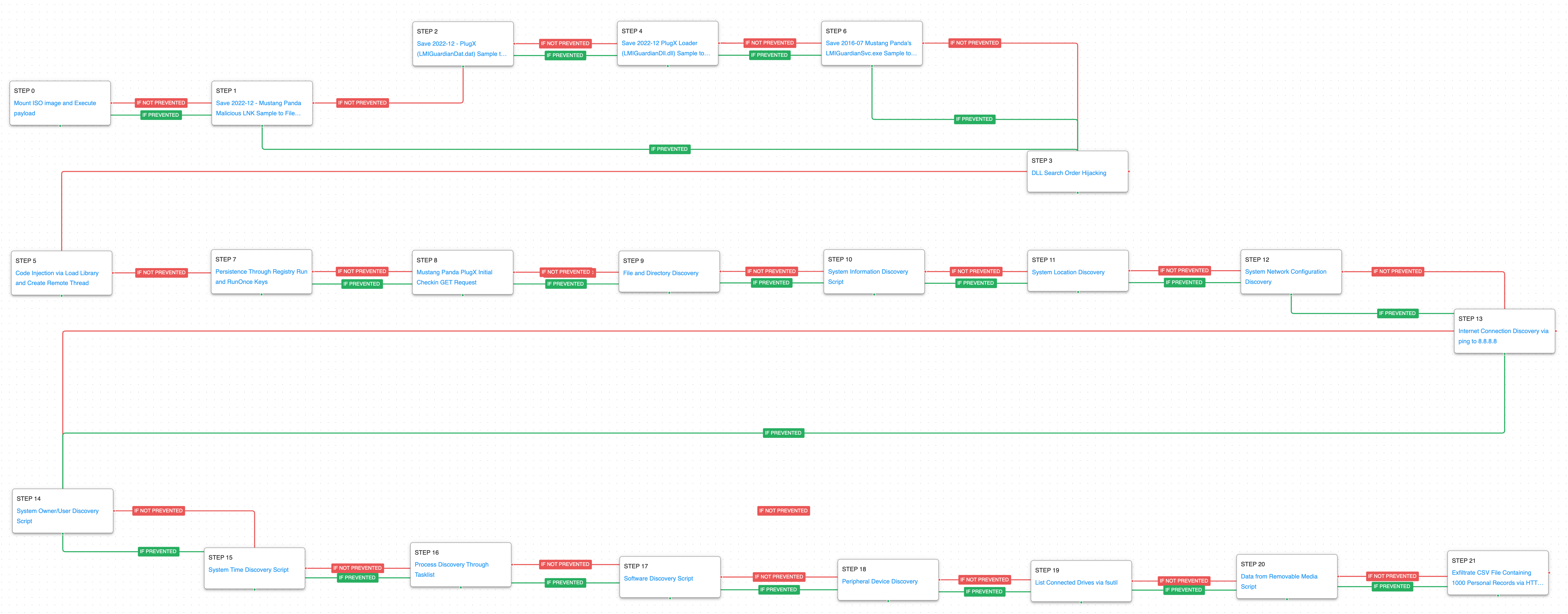
Mustang Panda – 2022-12 – European Commission-themed Lure leads to PlugX Infection
In December 2022, Mustang Panda was observed targeting multiple entities in Europe using a new custom variant of the PlugX backdoor. During this attack, the adversary used a malicious Optical Disc Image (ISO) file which after being double clicked is mounted and contains a Shortcut (LNK) file decoyed as a European Commission-themed document lure. This file is used to deploy PlugX leading to data exfiltration of sensitive information.
This attack graph starts by saving and mounting an ISO image file to execute the payload contained inside. Subsequently, a Shortcut file (LNK) is saved which subsequently drops 3 new files: a legitimate executable, the PlugX loader, and the encrypted PlugX malware. Then, the PlugX loader is executed via DLL Search Order Hijacking.
Subvert Trust Controls: Mark-of-the-Web Bypass (T1553.005): This scenario bypasses MOTW by downloading and mounting an ISO image on the system to execute the payload contained inside.
Ingress Tool Transfer (T1105): This scenario downloads to memory and saves to disk in two separate scenarios to test network and endpoint controls and their ability to prevent the delivery of known malicious content.
Hijack Execution Flow: DLL Search Order Hijacking (T1574.001): This scenario takes advantage of Microsoft’s Dynamic-Link Library (DLL) search order to load a rogue DLL into a system binary, leveraging the fact that the system binary will be often trusted by system administrators so that malicious code can run inside it without being examined.
In the second stage of the attack, malicious code is injected into an active process on the system and subsequently obtains persistence through Registry Run Keys. Communications with the adversary’s infrastructure is established which initiates the environment discovery stage.
Process Injection (T1055): This scenario injects a DLL file into another running process and validates if a canary file can be created.
Registry Run Keys / Startup Folder (T1547.001): The attack graph will attempt to create a new registry Run key to achieve persistence on the host.
Application Layer Protocol: Web Protocols (T1071.001): This scenario emulates the HTTP requests made by the PlugX backdoor by making an HTTP GET to an AttackIQ server that mimics the URL format and data sent by a real infection.
File and Directory Discovery (T1083): A batch script is executed that lists all files and directories in %ProgramFiles% and the %systemdrive%\Users directory.
System Information Discovery (T1082): The native systeminfo command is executed to retrieve all of the Windows system information.
System Location Discovery (T1614): The attack graph executes Windows native API calls to GetUserDefaultUILanguage, GetSystemDefaultUILanguage, and GetKeyboardLayoutList with the objective of language discovery of the system.
System Network Configuration Discovery (T1016): The network configuration of the asset is collected using standard Windows utilities like ipconfig, arp, route, and nltest.
Internet Connection Discovery (T1016.001): The actors used a ping to Google’s 8.8.8.8 DNS server to verify if they could connect to the internet.
Finally, in the last stage of the attack, final discovery actions are completed before exfiltrating the collected information.
System Owner / User Discovery (T1033): Live off the land by running whoami and users to gain details about the currently available accounts and permission groups.
System Time Discovery (T1124): The scenario identifies the time and time zone of the compromised system through the net time command.
Process Discovery (T1057): Window’s built-in tasklist command is executed as a command process and the results are saved to a file in a temporary location.
Software Discovery (T1518): A registry key containing entries for all the software installed on the victim asset. Reg.exe is used to access HKLM\Software\Microsoft\Windows\CurrentVersion\Uninstall.
Peripheral Device Discovery (T1120): This scenario retrieves information about systems peripherals such as logical drives, physical memory, network cards through the execution of commands and binaries.
Data from Removable Media (T1025): The native utility fsutil is used to identify any additional hard disks connected to the host. PowerShell is then used to iterate through every removable media device and harvest a list of files.
Exfiltration Over C2 Channel (T1041): A large amount of data is exfiltrated over HTTP requests mimicking the data exfiltration method used by the adversary.
Mustang Panda – 2022-05 – Global Phishing Campaign against Government Targets
Since March 2022, Mustang Panda has been observed carrying out global spearphishing attacks against the Government and Education sectors. During this activity, the adversary abused fake Google accounts to distribute malware via attachments or Google Drive links. The actor leveraged a newer malware family called TONESHELL and its loaders that so far have been reported to be exclusive to this threat actor. The goal of this attack graph is to establish a foothold and make the initial connections to the actor’s infrastructure.
This attack graph begins with the download and saving of a malicious ZIP file, which contains a legitimate executable and the TONEINS loader in DLL format. The executable main objective is to perform DLL Side-Loading. Persistence is obtained through a scheduled task named “ServiceHub.TestWindowStoreHost“.
Hijack Execution Flow: DLL Side-Loading (T1547.002): Bundles a DLL with a Windows executable that is susceptible to DLL Side-Loading to execute actor code.
Scheduled Task/Job: Scheduled Task (T1053.005): This scenario creates a new scheduled task using the schtasks utility.
In the second and final stage of the attack, TONESHELL is executed using DLL Side-Loading before the malware makes some simple discovery requests to identify the victim machine. The final step is a request to the actor’s command and control infrastructure to receive additional commands.
Windows Management Instrumentation (T1047): A WMI query used to retrieve the disk serial number: SELECT volumeserialnumber FROM win32_logicaldisk WHERE Name='C:'
Detection and Mitigation Opportunities
With so many different techniques being used by threat actors, it can be difficult to know which to prioritize for prevention and detection assessment. AttackIQ recommends first focusing on the following techniques:
1. Process Injection (T1055) and 2. DLL Side-Loading (T1547.002):
Both malware families are using techniques that obscure the true source of malicious activity. By either injecting into another process or using side-loading to load malicious code into a legitimate process actors can try to hide in normal system operating noise or abuse overzealous whitelisting:
1a. Detection
Searching for common processes that are performing uncommon actions can help identify when a process has been compromised. It would be uncommon for these processes to be executing additional process or performing discovery techniques. You can look for similar activity using a signature like:
Parent Process Name CONTAINS (‘explorer.exe’ OR ‘svchost.exe’)
Command Line CONTAINS (‘set’ OR ‘whoami’ OR ‘ping’ OR ‘dir’)
1b. Mitigation
2. Scheduled Task/Job: Scheduled Task (T1053.005)
Adversaries may abuse the Windows Task Scheduler to perform task scheduling for initial or recurring execution of malicious code. There are multiple ways to access the Task Scheduler in Windows. The schtasks utility can be run directly from the command line, or the Task Scheduler can be opened through the GUI within the Administrator Tools section of the Control Panel.
2a. Detection
With an EDR or SIEM Platform, you can detect the following commands being issued to schedule a malicious task:
Process Name = (“cmd.exe” OR “Powershell.exe”)
Command Line CONTAINS (“schtasks” AND “/CREATE” AND (“cmd” OR “powershell”)
2b. Mitigation
MITRE ATT&CK has the following mitigation recommendations:
- M1047 – Audit
- M1028 – Operating System Configuration
- M1026 – Privileged Account Management
- M1018 – User Account Management
Wrap-up
In summary, these attack graphs will evaluate security and incident response processes and support the improvement of your security control posture against another a prolific Chinese threat actor. With data generated from continuous testing and use of these attack graphs, you can focus your teams on achieving key security outcomes, adjust your security controls, and work to elevate your total security program effectiveness against a known and dangerous threat.
AttackIQ stands at the ready to help security teams implement this attack graph and other aspects of the AttackIQ Security Optimization Platform, including through our co-managed security service, AttackIQ Vanguard.

 (Click for Larger)
(Click for Larger) (Click for Larger)
(Click for Larger) (Click for Larger)
(Click for Larger) (Click for Larger)
(Click for Larger)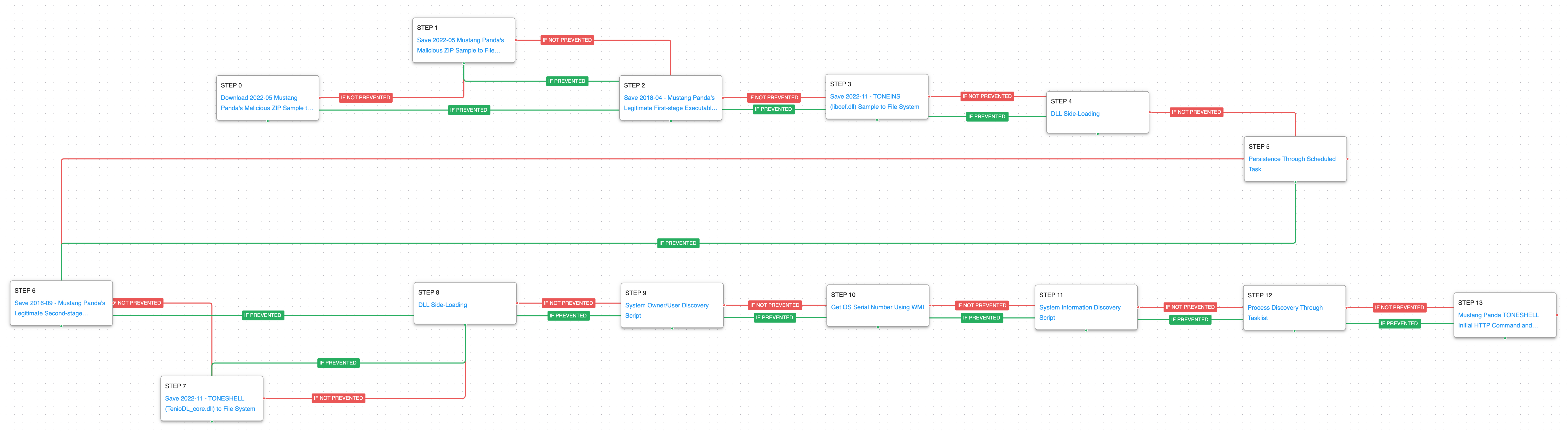 (Click for Larger)
(Click for Larger)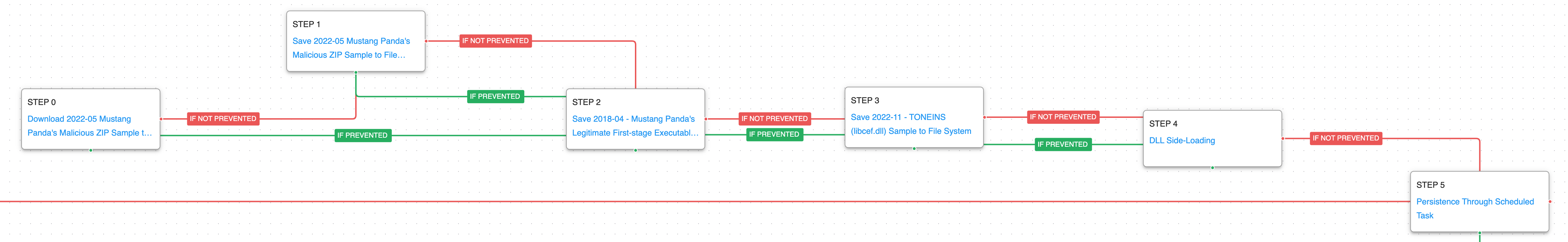 (Click for Larger)
(Click for Larger) (Click for Larger)
(Click for Larger)