Emotet continues to be used in wide broad-based attacks against victims in all sectors across all regions. First discovered in 2014 as a banking trojan, the malware has evolved to be one of the top malware-as-a-service threats and remains resilient against takedown efforts. In January 2021 the FBI partnered with global law enforcement agencies to attempt to take down the actors and infrastructure responsible for Emotet attacks but it only slowed them down for 11 months. The malware and actors resumed operations with a vengeance and rose back up to become one of the top malware families used in phishing attacks.
Emotet is primarily delivered via spear-phishing attacks and has shown flexibility and agility in changing attachment types for initial delivery to evade detection signatures. When a host is initially infected with Emotet it becomes part of their mass mailing botnet and will begin sending malicious emails to thousands of potential victims. After being abused to spread to more potential victims, access is sold to other threat actors whose own malware can then be downloaded through the command-and-control channels established through the initial Emotet infections.
AttackIQ has released two new attack graphs to emulate a pair of substantial Emotet attacks from last year to help customers validate their security controls and their ability to defend against similar campaigns. These attacks started with the delivery of malicious attachments and progressed into complete domain takeovers resulting in large scale data exfiltration and ransomware events.
Validating your security program performance against these behaviors is vital in reducing the risk of ransomware. By using these new attack graph(s) in the AttackIQ Security Optimization Platform, security teams will be able to:
- Evaluate security control performance against the initial access and discovery techniques that will be used prior to attacks from multiple threat actors.
- Assess their security posture against an ever-persistent malware family that has survived years of competition and take down attempts.
- Continuously validate detection and prevention pipelines against a malware strain that will continue to evolve and impact victims across the globe.
Emotet – 2022-05 – epoch5 Infection Chain leads to Data Exfiltration
The first attack graph emulates the behaviors observed by security researchers in a May 2022 attack that was delivered using a malicious Microsoft Office document from their epoch5 botnet. The graph starts with the delivery of Emotet and progresses to the dropping of Cobalt Strike and the network discovery actions taken by the actor to learn more about the infected environment. The end goal is to gain access to the Active Directory environment and exfiltrate sensitive data.
The first stage of the attack involves the delivery of the Emotet payload and its execution using RegSvr32. The malware achieves persistence using registry keys before collecting basic information about the infected asset. Emotet makes an initial HTTP request to their command-and-control server sending along the profiling data.
Ingress Tool Transfer (T1105): These scenarios download to memory and then save to disk in two separate steps to test network and endpoint controls and their ability to prevent the delivery of known malicious files. These scenarios are used for each stage of the malware delivered in these attacks.
System Binary Proxy Execution: Regsvr32 (T1218.010): RegSvr32 is a native Windows utility that threat actors can use to register Common Object Model (COM) DLLs. This functionality allows an actor to deploy a malicious DLL and have a native Windows tool execute the code as the parent process. This scenario executes RegSvr32 with an AttackIQ binary.
Logon Autostart Execution: Registry Run Keys (T1547.001): This scenario sets the HKCU\Software\Microsoft\Windows\CurrentVersion\Run registry keys that Windows uses to declare what applications should be run at system startup.
System Information Discovery (T1082): The native systeminfo command is executed to retrieve all of the Windows system information.
System Network Configuration Discovery (T1016): Native Window’s command, ipconfig, is executed to collect details about the infected host’s network adapters.
Application Layer Protocol: Web Protocols (T1071.001): This scenario emulates the HTTP traffic made by Emotet during an initial infection by making an HTTP GET request to an AttackIQ server that mimics the URL format and data sent in a real infection.
The next stage of the attack is emulating the delivery of the Cobalt Strike payload. This is executed using process hollowing and code injection into another running process.
Process Injection: Process Hollowing (T1055.012): A process is created in a suspended state and then its memory is unmapped and replaced with the contents of a malicious binary.
Process Injection: Dynamic-link Library Injection (T1055.001): This scenario injects a DLL file into another running process and validates if a canary file can be created.
The third stage of this attack graph is the execution of the different discovery techniques executed by the Cobalt Strike binary. Information about the local system’s accounts and mapped network shares are collected before pivoting to the Active Directory domain. The actor collected a list of domain computers and administrative accounts using native commands and a third-party utility.
Account Discovery: Local Account (T1087.001): A list of local accounts configured on this host is collected by executing the net user command. Knowing what other accounts are present on the host will allow the actor to potentially re-use previously known credentials or identify disabled legitimate accounts they can re-enable to blend in with everyday activity.
Network Share Discovery (T1135): The threat actors leveraged the Invoke-ShareFinder cmdlet from Veil-PowerView to identify remote network shares that could contain files of interest. Alternatively, they executed native the net share command to retrieve the same information.
Permission Groups Discovery: Domain Groups (T1069.002): The Domain Computers group is collected to identify a list of computers joined to the enterprise domain using the net group command.
Account Discovery: Domain Account (T1087.002): The system command net group is used to list Domain and Enterprise Admins accounts. The Adfind utility is also used to discover details about the victim’s Active Directory configuration including accounts, groups, computers, and subnets.
Domain Trust Discovery (T1482): This scenario calls the native nltest utility with the /trusted_domains option to retrieve a list of trusted Active Directory domains associated with this host.
The final stage of this graph focuses on moving laterally to additional systems and exfiltrating sensitive data.
Steal or Forge Kerberos Tickets: Kerberoasting (T1558.003): Kerberoasting allows an attacker to attempt to extract password hashes for user accounts with a Service Principal Name (SPN) assigned .
System Services: Service Execution (T1569.002): PAExec is used to execute a command on a remote host by creating a temporary Windows service.
Exfiltration Over C2 Channel (T1041): Files are sent to an AttackIQ controlled server using HTTP POST requests.
Emotet – 2022-06 – Cobalt Strike and Mimikatz used to deploy Quantum Ransomware
The second attack graph covers activity that occurred one month later, this time Emotet was delivered using a malicious shortcut (LNK) file. Many of the same behaviors were observed in this campaign and once again Cobalt Strike was delivered as the secondary payload. However, the final goal was the deployment of the Quantum ransomware after exfiltrating data and extorting the victim.
The first stage of the attack follows the same pattern observed in the epoch5 attack for the delivery of the Emotet but using a shortcut file that executes PowerShell code. Emotet is executed with RegSvr32, and persistence established with another registry run key. The malware performs the same initial discovery techniques before moving on to their secondary payload.
Cobalt Strike is downloaded and executed using process injection before evaluating its privileges by using named pipes to impersonate a system level access token. The actor performs hands on keyboard exploration of the victim’s Active Directory environment before attempting to dump credentials with Mimikatz.
Access Token Manipulation: Token Impersonation/Theft (T1134.001): A named pipe is a block of shared memory in Windows that enables two unrelated processes to communicate data between themselves. One process acts as a server, registering the named pipe and listening for a connection. A second process is the client that can then send data to the named pipe which is picked up by the server. It is possible for the server component to impersonate the client’s security context by using the ImpersonateNamedPipeClient Windows API function once the client connects.
OS Credential Dumping: LSASS Memory (T1003.001): Mimikatz is used to dump additional credentials from the LSASS process memory that would aid the actor in moving to additional hosts.
Before moving laterally, the actor attempts to use AdFind to learn more about the other hosts inside the enterprise domain before scanning for any hosts with file sharing or remote desktop enabled. The actor was observed both using WMI commands to execute commands on remote machines as well as using Remote Desktop to have graphical access to additional hosts.
Network Service Discovery (T1046): This scenario uses nmap for scanning hosts that are open on ports 139,389,445,636,3389 that would identify remotely accessible hosts to the attacker.
Windows Management Instrumentation (T1047): This scenario uses wmic commands to execute commands on a remote target.
Remote Services: Remote Desktop Protocol (T1021.001): Remote Desktop is the built-in remote access utility used by Windows. This scenario attempts to remotely connect to another accessible asset with stolen credentials.
The final stage of the attack involves the rapid collection of files of interest before exfiltrating data over HTTP. Quantum ransomware is downloaded to the infected host and executed using RunDll32. Files are encrypted with a ransomware similar to Conti.
Data Staged: Local Data Staging (T1074.001): Files are collected and stored in a temporary directory so they can be exfiltrated later.
System Binary Proxy Execution: Rundll32 (T1218.011): RunDll32 is a native system utility that can be used to execute DLL files and call a specific export inside the file. This scenario executes RunDll32 with an AttackIQ DLL and calls an export to mimic previously reported malicious activity.
Data Encrypted for Impact (T1486): AttackIQ has replicated the functionality used by a similar ransomware, Conti, to encrypt files on the targeted hosts. This includes the common file extensions and encryption methods utilized by the actor.
Detection and Mitigation Opportunities
With so many different techniques being used by threat actors, it can be difficult to know which to prioritize for prevention and detection assessment. AttackIQ recommends first focusing on the following techniques emulated in our scenarios before moving on to the remaining techniques.
1. Logon Autostart Execution: Registry Run Keys (T1547.001):
Preventing an actor from maintaining a foothold in your environment should always be one of the top priorities. In both campaigns, Registry Run keys were used to keep Emotet running after a reboot. The actor’s abused their access over multiple days and a simple reboot would have prevented their actions if the persistence couldn’t be established.
1a. Detection
Using a SIEM or EDR Platform to see modifications to the Run and RunOnce keys will alert when unauthorized users or software makes modifications to the keys that allow programs to run are startup.
Process Name == reg.exe
Command Line Contains (“ADD” AND “\CurrentVersion\Run”)
1b. Mitigation
MITRE ATT&CK does not have any direct mitigations as this is abusing legitimate Windows functionality. They recommend monitoring registry changes and process execution that may attempt to add these keys.
2. System Binary Proxy Execution: Regsvr32 (T1218.010)
Emotet was executed using the native Windows utility Regsvr32 as it was commonly delivered as a DLL file.
2a. Detection
While this native tool is commonly used by legitimate applications there are behaviors related to their execution that can stand out in your process logs. Searching for files that are being executed from temporary directories, that don’t have the standard .dll file extension, or call strange looking export names can stand out from regular user behavior.
Process Name == regsvr32.exe
Command Line CONTAINS (‘TEMP’ OR ‘.png’ OR ‘Roaming’)
2b. Mitigation
3. Process Injection (T1055)
Malware will commonly inject malicious code into other running processes to attempt to blend in with legitimate applications.
3a. Detection
Searching for common processes that are performing uncommon actions can help identify when a process has been compromised.
3b. Mitigation
Wrap-up
In summary, these attack graphs will evaluate security and incident response processes and support the improvement of your security control posture against another cybercrime malware family that facilitates intrusions from many different threat actors. With data generated from continuous testing and the use of these attack graphs, you can focus your teams on achieving key security outcomes, adjust your security controls, and work to elevate your total security program effectiveness against a known and dangerous threat.
AttackIQ stands at the ready to help security teams implement this attack graph and other aspects of the AttackIQ Security Optimization Platform, including through our co-managed security service, AttackIQ Vanguard.

 (Click for Larger)
(Click for Larger)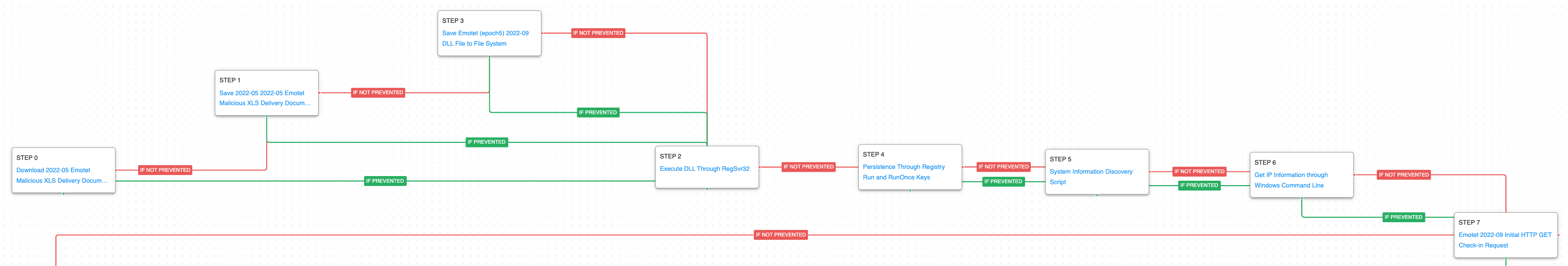 (Click for Larger)
(Click for Larger)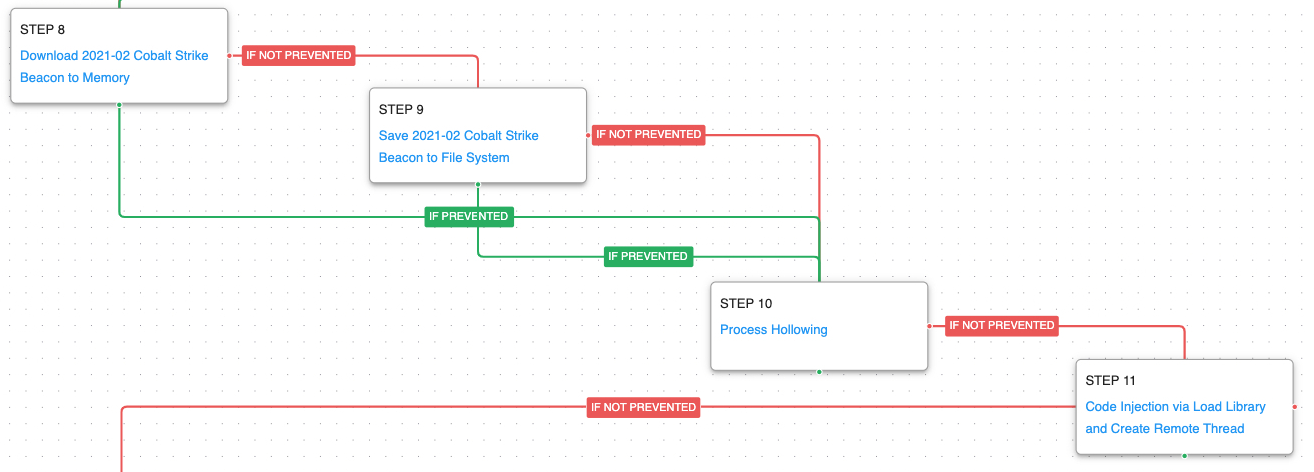 (Click for Larger)
(Click for Larger) (Click for Larger)
(Click for Larger) (Click for Larger)
(Click for Larger)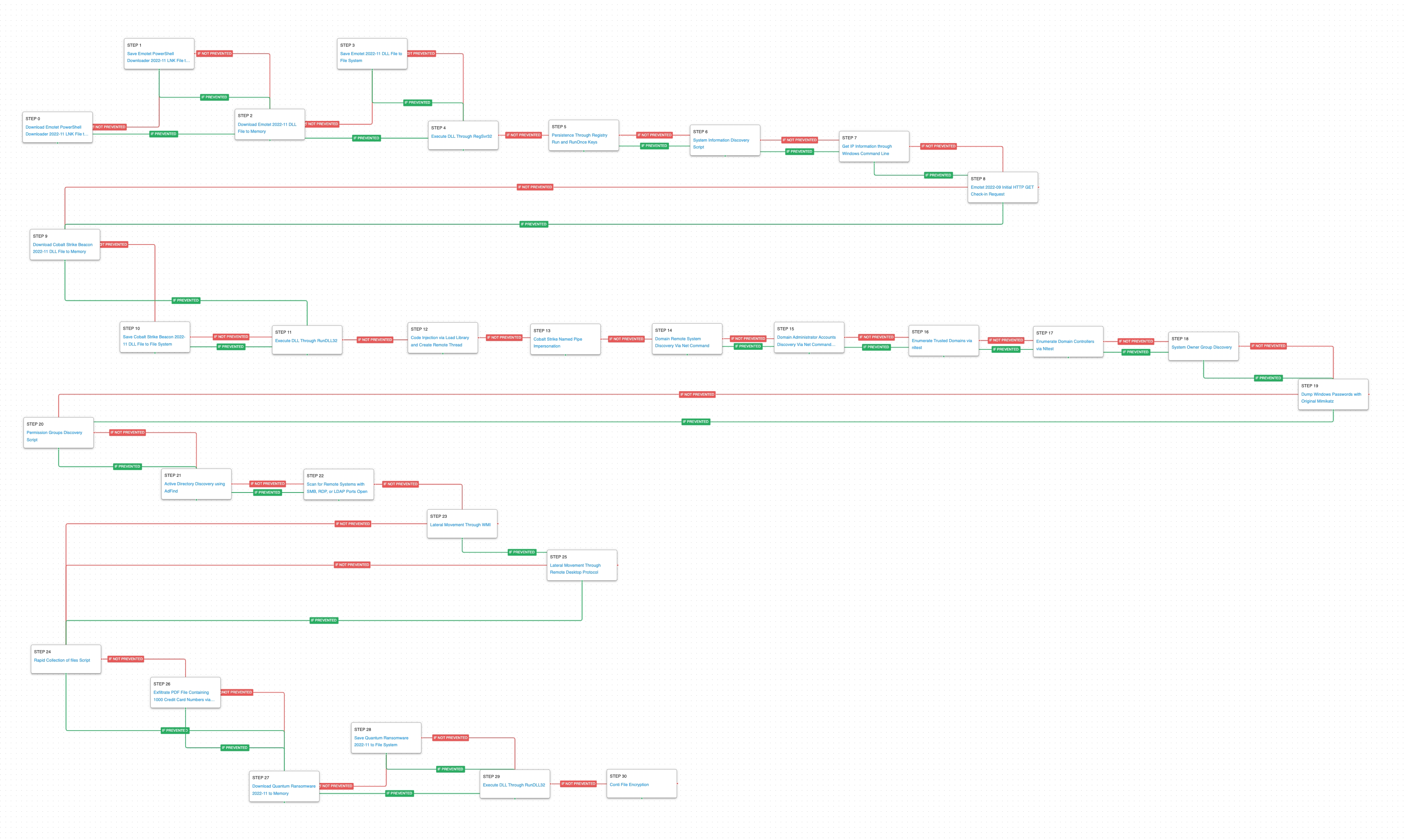 (Click for Larger)
(Click for Larger) (Click for Larger)
(Click for Larger)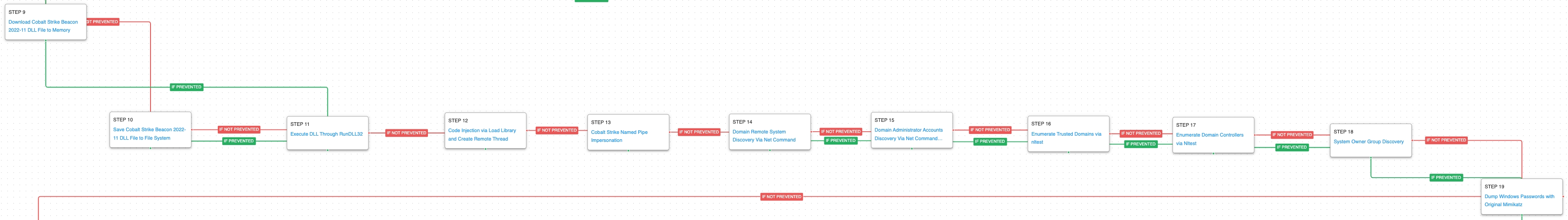 (Click for Larger)
(Click for Larger)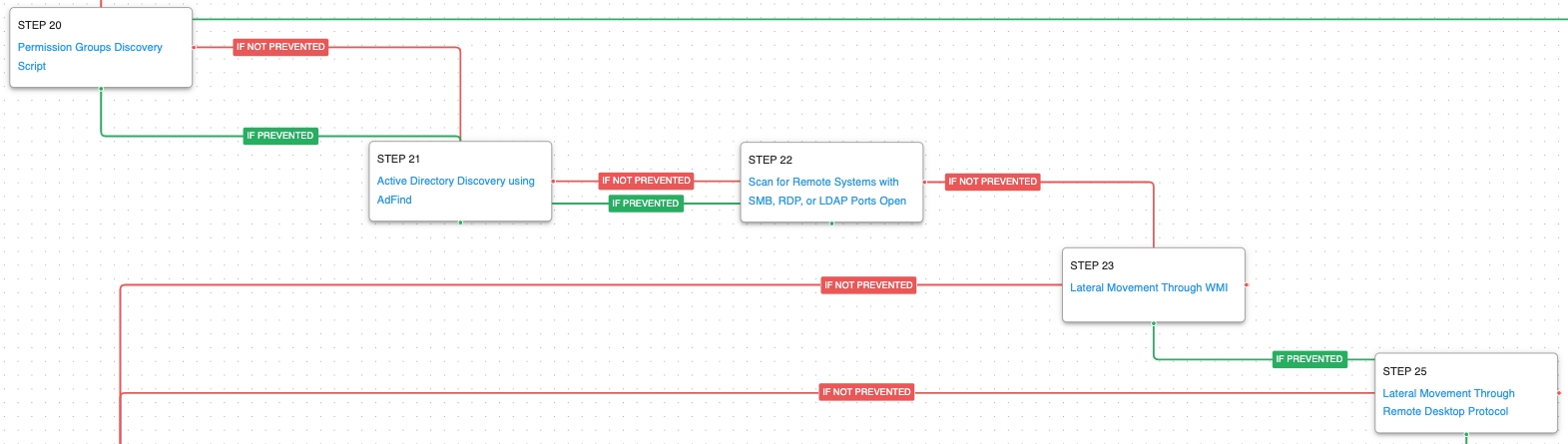 (Click for Larger)
(Click for Larger) (Click for Larger)
(Click for Larger)