AsyncRAT is an open-source Remote Access Trojan (RAT) written in .NET and designed for Windows systems that was first published on Github in January 2019. It is capable of remotely monitoring and controlling compromised systems through a secure encrypted connection allowing the attacker to perform a variety of actions, such as keylogging, audio/video recording, info-stealing, password collection, data exfiltration, remote command execution, dropping and executing additional payloads, among other functions.
The malware has been used extensively by multiple adversaries since its inception, either as is or in a customized form. Furthermore, AsyncRAT has been observed engaging in a wide range of activities that include the use of spear phishing attachments and script loaders for its delivery.
AttackIQ has released a content bundle consisting of two attack graphs that bring together the post-compromise Tactics, Techniques, and Procedures (TTPs) exhibited by AsyncRAT during its latest activities to help customers validate their security controls and their ability to defend against this threat.
Validating your security program performance against these behaviors is vital to reducing risk. By using these new attack graphs in the AttackIQ Security Optimization Platform, security teams will be able to:
- Evaluate the performance of security controls against multiple threat actors that utilize AsyncRAT as their preferred choice to gain foothold into the system.
- Assess their security posture against one of the most prolific malware families used by cybercrime.
- Continuously validate detection and prevention pipelines against a widely distributed threat.
AsyncRAT – 2023-03 – From OneNote Phishing Through HTML Application (HTA) to Malware Deployment
In March 2023, the Splunk Threat Research Team (STRT) released a report uncovering a phishing campaign that featured malicious OneNote (.ONE) attachments. These documents were used to lure the target into clicking on a pop-up warning to presumably view the content but, in turn, loads a malicious HTML Application (HTA) file that downloads and executes an obfuscated batch (BAT) script that ultimately decodes, loads and executes AsyncRAT.
This stage begins with downloading and saving a malicious OneNote document that is used to load and execute a Microsoft HTML Application (HTA) file via the MSHTA utility.
This HTA is responsible for downloading a batch script, which subsequently drops a PowerShell script that performs the deployment of AsyncRAT.
Ingress Tool Transfer (T1105): These scenarios download to memory and save to disk in two separate scenarios to test network and endpoint controls and their ability to prevent the delivery of known malicious content.
System Binary Proxy Execution: Mshta (T1218.010): This scenario utilizes the Mshta.exe Windows utility to execute a local HTML Application (HTA) file.
At this stage, AsyncRAT is deployed and executed on the system. Then, it attempts to achieve persistence through the creation of a scheduled task, and if this fails, registry run keys are used as an alternative.
Subsequently, it leverages SeDebugPrivilege to gain more privileges and control over other processes. Finally, it verifies the presence of a virtualized environment through Windows Management Instrumentation (WMI) objects.
Scheduled Task/Job: Scheduled Task (T1053.005): This scenario attempts to create a new scheduled task for persistence using the schtasks utility.
Boot or Logon Autostart Execution: Registry Run Keys (T1547.001): This scenario acquires persistence by setting the HKLM\Software\Microsoft\Windows\CurrentVersion\Run registry key that Windows uses to identify what applications should be run at system startup.
Access Token Manipulation (T1134): This scenario enables the SeDebugPrivilege privilege for the current process using the AdjustTokenPrivilege Windows API.
System Information Discovery (T1082): This scenario executes the Get-WmiObject Win32_ComputerSystem via PowerShell to obtain detailed information pertaining to the compromised host.
AsyncRAT – 2023-09 – HTML Smuggling Leads to Full Infection via Visual Basic Script (VBS)
In October 2023, eSentire reported that at the beginning of September 2023, it had identified an infection chain associated with the Remote Access Trojan (RAT) known as AsyncRAT. During these activities, AsyncRAT was being delivered through phishing emails utilizing the HTML Smuggling technique, which allows the attacker to hide and deliver malicious code to a victim’s browser using seemingly benign HyperText Markup Language (HTML) and JavaScript by tricking a web application into loading and executing malicious JavaScript code.
This stage begins with the deployment of a malicious PowerShell script responsible for downloading a Visual Basic Script (VBS) file, which is then executed by a scheduled task. Subsequently, the VBS continues with the download and saving of an additional PowerShell Script that is responsible for deploying AsyncRAT.
Command and Scripting Interpreter: Visual Basic (T1059.005): This scenario will attempt to execute a Visual Basic Script (VBS) via cscript.exe.
Obfuscated Files or Information: Encrypted/Encoded File (T1027.013): This scenario encodes a user-defined PowerShell script into base64 and then executes it using PowerShell’s -encodedCommand and -ExecutionPolicy Bypass parameters.
At this stage, AsyncRAT is deployed and executed on the system using process hollowing. Then, it attempts to achieve persistence through the creation of a scheduled task, and if this fails, registry run keys are used as an alternative.
Subsequently, it leverages SeDebugPrivilege to gain more privileges and control over other processes. Finally, it verifies the presence of a virtualized environment through Windows Management Instrumentation (WMI) objects.
Process Injection: Process Hollowing (T1055.012): This scenario creates a process in a suspended state, then its memory is unmapped and replaced with the contents of the malicious executable. In this way, code execution is masked under a legitimate process.
Detection and Mitigation Opportunities
Given the vast number of techniques used by this threat, it can be difficult to know which to prioritize for prevention and detection assessment. AttackIQ recommends first focusing on the following techniques emulated in our scenarios before moving on to the remaining techniques.
1. Process Injection (T1055):
Malware will commonly inject malicious code into legitimate running processes to attempt to blend in with legitimate applications to remain hidden and appear normal to the compromised system.
1a. Detection
Searching for common processes that are performing uncommon actions can help identify when a process has been compromised.
1b. Mitigation
MITRE ATT&CK recommends the following mitigation recommendations:
2. Scheduled Task/Job: Scheduled Task (T1053.005)
Adversaries may abuse the Windows Task Scheduler to perform task scheduling for initial or recurring execution of malicious code. There are multiple ways to access the Task Scheduler in Windows. The schtasks utility can be run directly from the command line, or the Task Scheduler can be opened through the GUI within the Administrator Tools section of the Control Panel.
2a. Detection
With an EDR or SIEM Platform, you can detect the following commands being issued to schedule a malicious task.
Process Name = (“cmd.exe” OR “Powershell.exe”)
Command Line CONTAINS (“schtasks” AND “/CREATE” AND (“cmd” OR “powershell”)
2b. Mitigation
MITRE ATT&CK has the following mitigation recommendations for Scheduled Task
- M1047 – Audit
- M1028 – Operating System Configuration
- M1026 – Privileged Account Management
- M1018 – User Account Management
3. Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder (T1546.001):
Preventing an actor from maintaining a foothold in your environment should always be one of the top priorities. During these activities, the adversary used registry keys to achieve persistence.
3a. Detection
Using a Security Information and Event Management (SIEM) or Endpoint Detection and Response (EDR) Platform to see modifications to the Run and RunOnce keys will alert when unauthorized users or software makes modifications to the keys that allow programs to run after startup.
Process Name = reg.exe
Command Line CONTAINS (“ADD” AND “\CurrentVersion\Run”)
3b. Mitigation
MITRE ATT&CK does not have any direction mitigations as this is abusing legitimate Windows functionality. They recommend monitoring registry changes and process execution that may attempt to add these keys.
Wrap-up
In summary, these attack graphs will help organizations evaluate security and incident response processes and support the improvement of your security control posture against AsyncRAT. With data generated from continuous testing and use of these attack graphs, you can focus your teams on achieving key security outcomes, adjust your security controls, and work to elevate your total security program effectiveness against a known and dangerous threat.
AttackIQ offers a comprehensive Breach and Attack Simulation Platform to assist security teams. This includes AttackIQ Flex, a tailored pay-as-you-go service; AttackIQ Ready!, a fully managed service for continuous security optimization; and AttackIQ Enterprise, a co-managed service offering enhanced support. These services ensure your team maintains a robust security posture.

 Click for larger
Click for larger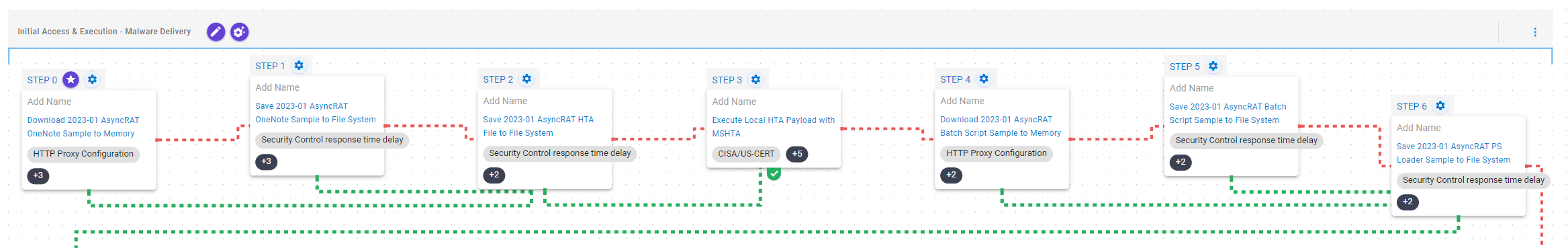 Click for larger
Click for larger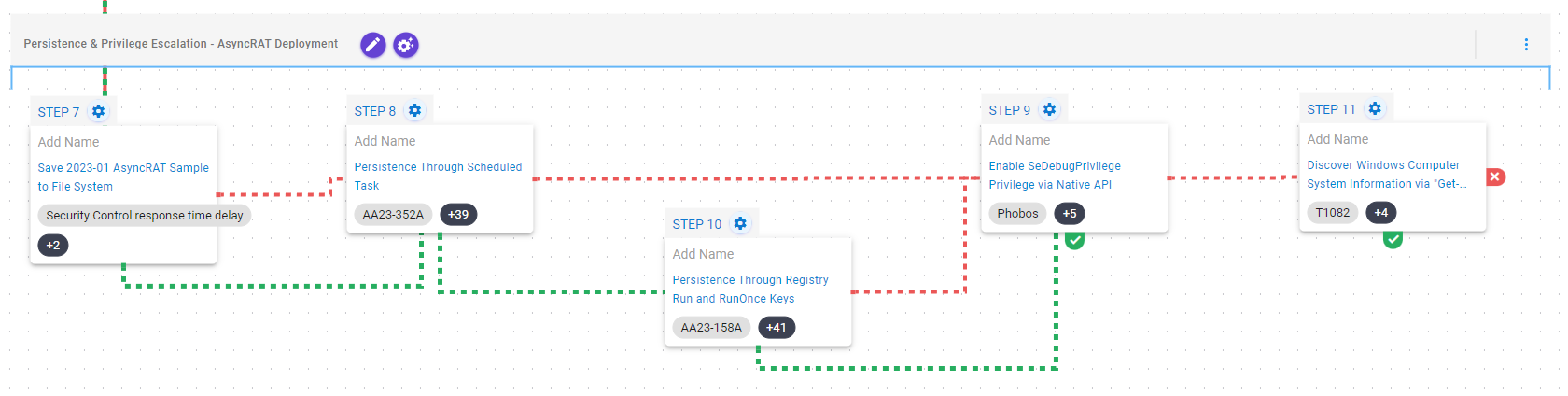 Click for larger
Click for larger Click for larger
Click for larger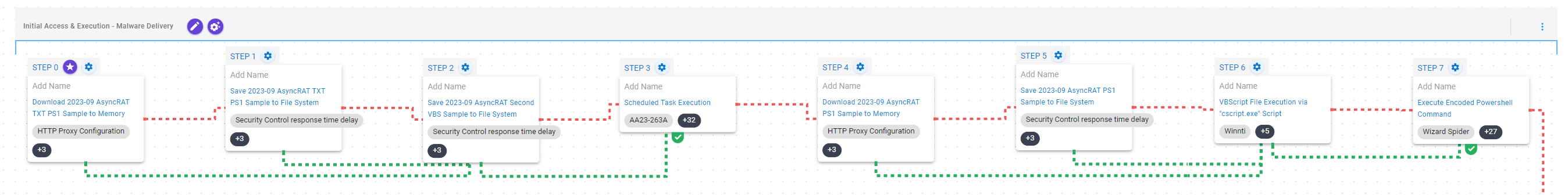 Click for larger
Click for larger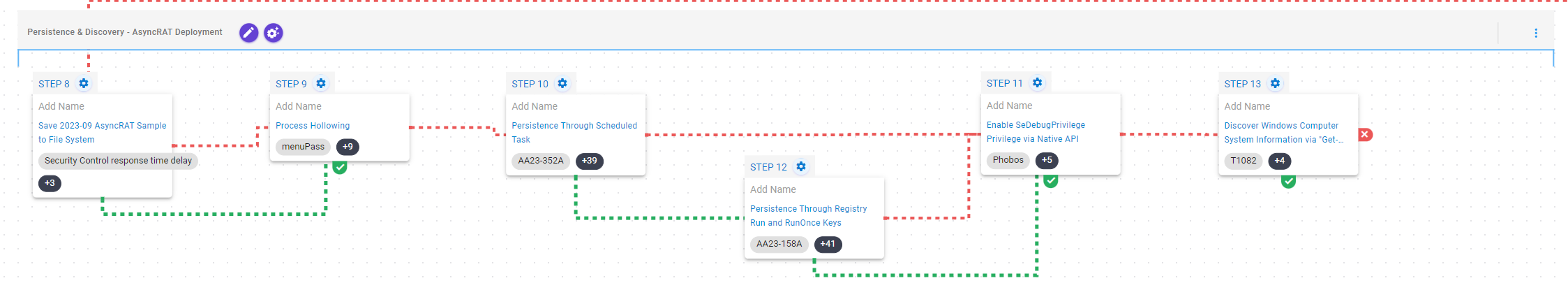 Click for larger
Click for larger