Summary:
AttackIQ now integrates with Vectra AI, a network detection and response tool. Utilize AttackIQ’s PCAP replays, DNS lookup or other network related scenarios to test the efficacy of the tool. In this blog, we will explore an atomic DNS lookup, a PCAP replay testing SQL injection and a PCAP replay exploring a Kerberos Domain Enumeration attack.
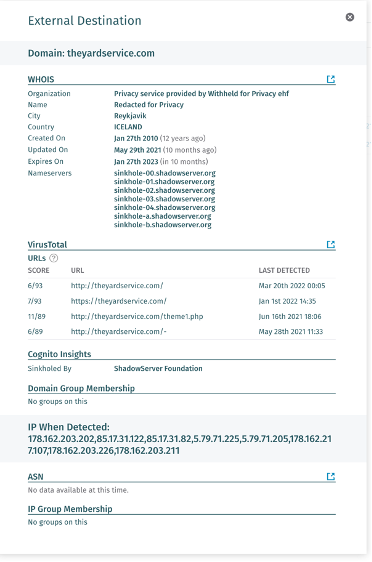
Scenario #1 – theyardservice.com DNS Lookup
The purpose of this scenario is to make connection to theyardservice[.]com which is a known APT29 phishing campaign DNS. In a real world scenario, a user may click the link and initiate a malware download. Utilizing a network control, one can block the destination from ever downloading. Vectra gives us more insight into what DNS calls are being made as we can see here:
Our integration will now take this detection and parse out any notables. The best notable for us to use is the domain name as it is a clear indicator that will match against the scenario.
As shown below, we now have a detection correlated with Vectra. The raw event is displayed as well showing the domain, theyardservice[.]com, as present within the event.


DNS Lookup scenarios are reliable ways to validate domain blocking within your network. If a connection is successful to a malicious C&C server, payload downloads may be attempted which may then lead to further exploitation along the chain. Stopping malicious downloads at the source before a payload download can be initiated should be a priority as underlying security controls may break down.
Scenario #2 – PCAP Replay – SQL Injection Attack
The purpose of this scenario is to test prevention controls against a SQL injection, a common attack found within OWASP top 10. This scenario will replay three injections over port 80 from an attacking server to a target. Below you can see the topology used:


Below, we can see the detection within Vectra’s UI. Vectra is able to capture the exact SQL fragment that is being used which we can then utilize to correlate our detection.

Now that Vectra has shown to detect this PCAP replay, our integration will pull back this information and parse out the various indicators. A combination of host information and information about the attack are matched against:

Scenario #3 – PCAP Replay – Kerberos Account Enumeration
This scenario will attempt to send TGT (Ticket Granting Ticket) requests without any pre-authentication to a Key Distribution Center (KDC) on port 88.
A TGT is a ticket assigned to each user that is then used to authenticate to the KDC which handles the actual authentication and distribution of tickets. Think of this as your seat within a sports stadium. As you enter, you present your ticket (TGT) to the attendant (KDC) and they will let you into the stadium. With Kerberos enumeration, an attacker will repeatedly present their ticket to the KDC hoping to retrieve domain user information. The PCAP replay uses pre-authentication to bypass any checks that a DC would make. With pre-authentication removed from the equation, an attack can be launched from a non-domain joined machine so long as it has access to the KDC.
Now that we have launched our scenario, we can see the Vectra has properly detected the attack:

Our platform utilizes the time of the detection and asset information to correlate:


Using the above three scenarios is a great quick test to validate both the integrations health and the health of Vectra.AI. AttackIQ is also releasing assessment templates for both Windows and Linux which will further allow you to test efficacy. For more details, contact your AttackIQ channel partner, AE or customer success manager. To see this integration in action, register for our demo on May 5th.






