With the recent release of the Security Stack Mappings by the MITRE Engenuity Center for Threat-Informed Defense, consumers are now able to overlay native Microsoft Azure security controls against MITRE ATT&CK.
For the first time, organisations can visually see what Azure security controls can offer in terms of protection, detection and response. With 45 native Azure security control mappings, defenders can start focusing on not only TTPs in the context of Azure threats, but also how each native Azure security control might shield them from related TTPs in Azure.

Figure 1: Azure Stack Mappings coverage shown using ATT&CK Navigator
Similar to MITRE ATT&CK, the Security Stack Mappings is subjective in nature. The size, budget, risk, compliance and threat model are just some of the factors that an organisation may wish to consider when assessing which native security controls are more important and relevant to their business requirements. Understanding how adversary behaviours and TTPs align to Azure security controls using ATT&CK, helps organizations focus their defensive efforts by determining which controls may be better suited for different types of threats. Adopting a purple teaming strategy can also aid in not only developing countermeasures for Azure, but also to continually test the security controls’ efficacy via threat emulation.
Ransomware and Azure
Although there hasn’t been an abundance of ransomware targeting Azure specifically in the public domain, it is fair to assume that as cloud service providers (CSPs) continue to evolve in complexity, and as cloud migration projects continue to trend upwards, Microsoft Azure and other CSPs will likely see an increase of ransomware attacks in the future.
As Microsoft explained in a past blog post, many of the human operated and more advanced threat actors they observed are typically using similar tactics and techniques prior to dropping their final ransomware payload.
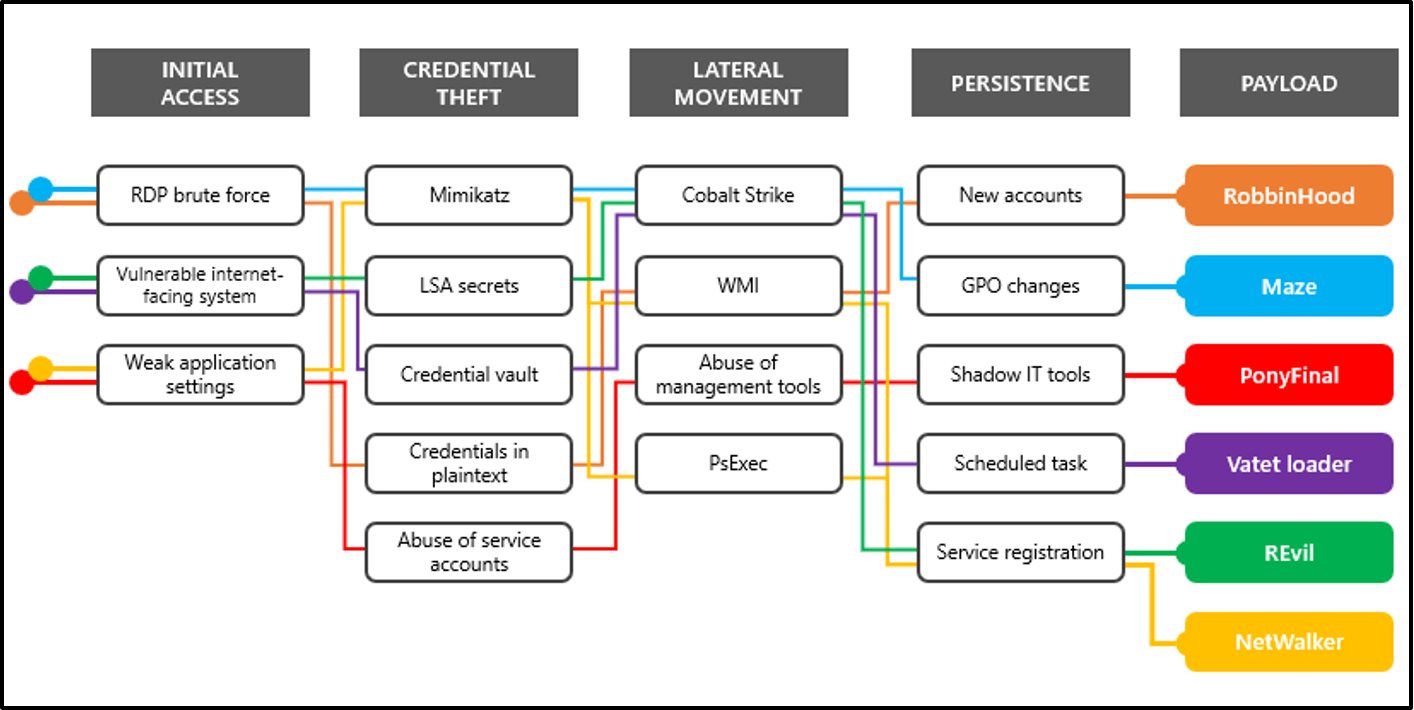
Figure 2: Common ransomware attack tactics and techniques (source: Microsoft)
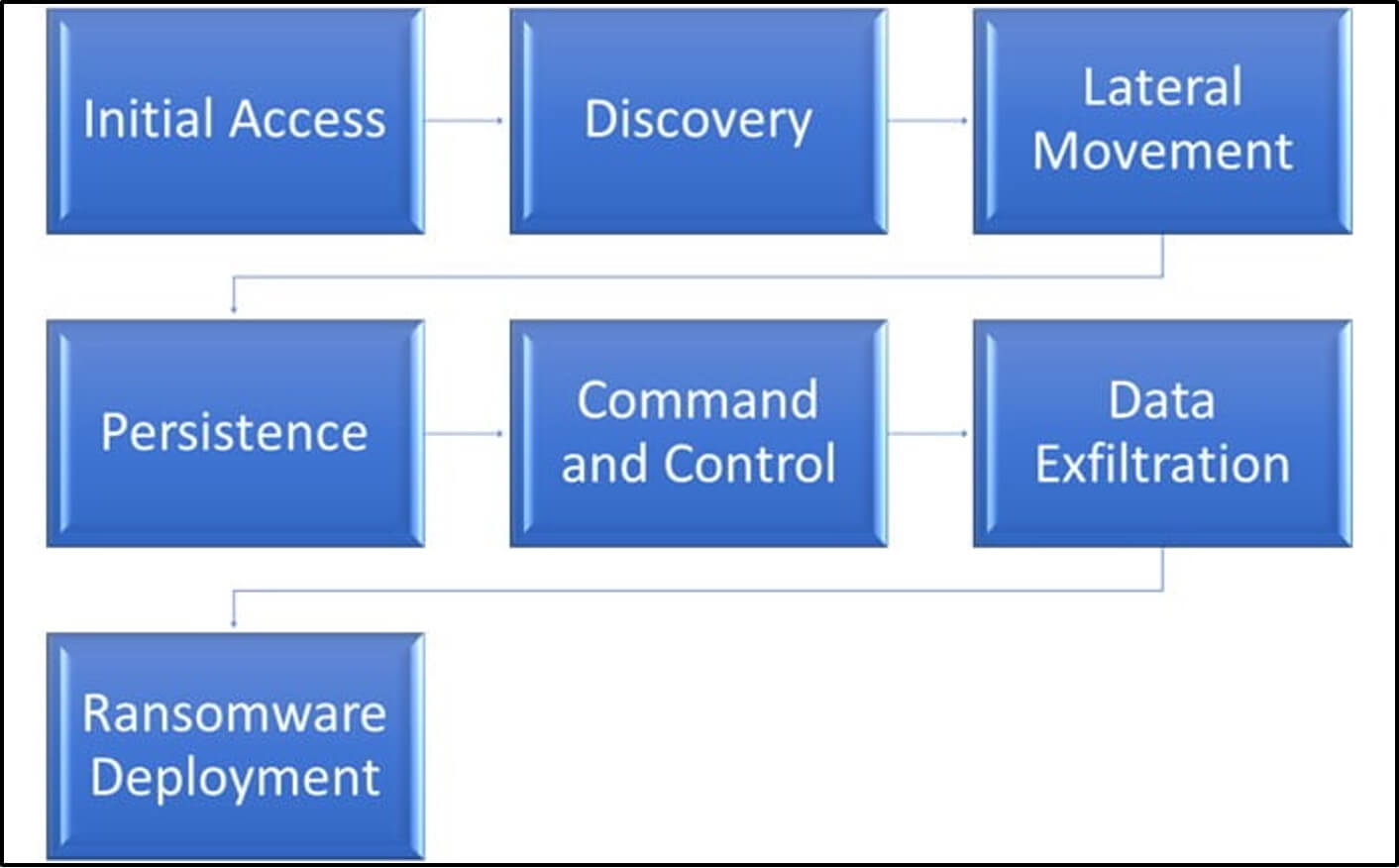
Shown in the above diagram, moving from initial access to credential theft, lateral movement and persistence, are some of the common precursors observed with some of the more well known ransomware groups, as well as less sophisticated attackers. Secureworks report similar attack phases as shown in the diagram below.
So how might one go about using the Security Stack Mappings to assess which native Azure security controls you should prioritize, particularly surrounding ransomware? As mentioned earlier, the security stack mappings is subjective in nature, but the good news is that there are some clear first steps one can take to try to solidify your understanding of which security controls are relevant for your organisation in the context of ransomware.
Step 1: Understand your native Azure Security Controls
Before beginning your journey into exploring the Security Stack Mappings, you first need to understand which native security controls you have in your Azure environment. This might sound trivial, but knowing which security controls you have at your disposal can help you to narrow your scope of which ransomware ATT&CK TTPs are relevant and/or important to you. AttackIQ has built on MITRE Engenuity’s Azure Mappings research in this white paper and presentation to help you begin to understand the controls resident in Azure. As an example, Azure Backup aligns to the ATT&CK “impact” tactic, specifically for the “defacement” and “disk wipe” techniques. Azure Backup helps with responding to a ransomware attack, whereby a threat actor may have successfully managed to delete and/or encrypt files, folders or entire virtual machines.
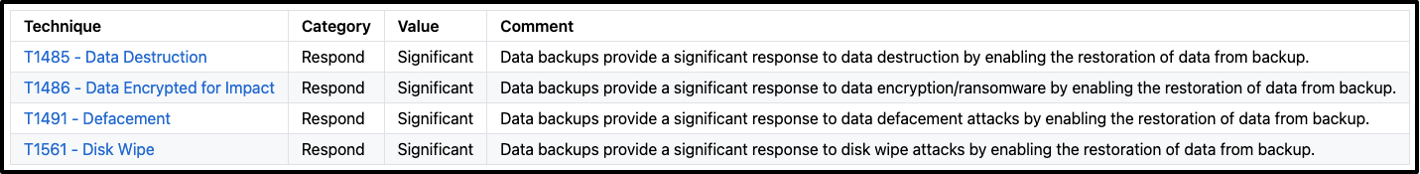
Figure 3: Technique coverage for Azure Backup (Security Stack Mappings)
Understanding your backup policies, what assets are being backed up, how frequently and where the backups are being sent to, soft delete retention policies, as well as testing your disaster recovery strategy are just some examples of how to think about this particular security control in the context of ransomware. As Azure Backup aligns to the Respond category of “protect, detect, respond”, the questions will likely surround the worst case scenario of “what if a ransomware operator deleted our backups and/or encrypted our files,” Understanding which security controls you have in your environment will likely produce a unique set of questions that surround that given security control, and in itself can produce lots of constructive discussion and things to consider.
Step 2: ATT&CK Left to Right
Attacks often start with initial access. Using the Security Stack Mappings, you could focus your efforts on the External Remote Services (T1133) technique. This technique into the initial access and persistence tactics, so offers a two-for-one deal in that preventing and detecting this technique with the right controls not only reduces your attack surface during initial access, but can also prevent longer-term persistence mechanisms. Referring to the Security Stack Mappings, you can start to narrow down your scope in the context of how a ransomware actor might operate in your Azure environment. For this technique alone, the following Azure security controls are listed:
- Azure AD Identity Secure Score
- Azure Alerts for Network Layer
- Azure Firewall
- Azure Network Traffic Analytics
- Azure Policy
- Azure Security Center Recommendations
- Cloud App Security Policies
- Just-in-Time VM Access
- Microsoft Defender for Identity
- Network Security Groups
You can continue to focus on specific Azure-aligned techniques to narrow down your list of controls. As you move left-to-right along the MITRE ATT&CK tactics, you can start to think about what TTPs you may want to prioritize over others, and which ones are more or less relevant to you. As mentioned in the first approach, understanding which controls you have will potentially help you to filter the controls relevant to you.
For example, if you only have Azure Firewall available, you can use the External Remote Services TTP to check that your firewall is allowing and denying traffic based on your business and security requirements. This in itself could considerably reduce your attack surface by allowing you to focus on ways to prevent certain network traffic, such as remote access software, exfiltration, or traffic over non-standard ports. If an Azure environment is not sufficiently locked down, someone could potentially spin up a virtual machine with unrestricted access, bypassing your security policy entirely.
Step 3: Prevent vs. Detect vs. Respond?
Expanding on the above two examples, by now you may know exactly what Azure security controls as well as what ransomware specific TTPs you wish to focus on. One of the valuable ways to use the Security Stack Mappings is to see how each control aligns to a particular category. The three categories are:
- Protect
- Detect
- Respond
Depending on the TTPs you’re interested in, each control may offer a combination of protection, detection and/or response. Ultimately, not all threats may necessarily be prevented due to the nature of what the particular TTP is doing. For example, some TTPs in the discovery tactic are not always preventable, but can still be detected. Perhaps you are currently going through a cloud migration project to Azure, and perhaps you don’t yet have many security controls just yet. In which case, concentrating on detection may be a good place to start. Azure Sentinel offers a great deal of detections for many TTPs in Azure.
Step 4: Threat-informed Prioritization
The last approach is somewhat dependent on your security maturity and security optimization program. Working under a threat-informed strategy help you make better decisions about which threats may be relevant to your organization as well as your industry sector. Perhaps your CTI team has observed particular TTPs that aren’t listed on the security stack mappings or ATT&CK. Or perhaps your defenders have seen a recent flurry of undocumented TTPs in your organisation, which could be malicious threat actor activity, or activity generated from your red team operations. Researching and understanding new as well as existing TTPs will help to build knowledge and assess potential gaps in your native security controls in the long-term.
Closing Thoughts
So what are the top native security controls for Azure? Like so often in cybersecurity, the answer is ultimately, “it depends”.
It depends on which native security controls you have in your Azure environment. It depends on which ransomware TTPs are of a concern to you. It depends whether you are focusing on prevention, detection, or response. And it may also depend on whether your CTI or blue team is collecting to determine the threat actors that pose a threat to your organisation.
Despite these questions, given their overarching importance to security in the cloud, Azure Backup, Azure Firewall, and Azure Sentinel are good places to start. While there is never a one-size-fits-all approach, reviewing the security controls you have, along with the security stack mappings and ransomware TTPs of interest to you, will help you to start thinking about how you can prevent, detect, and respond to ransomware threats in Azure. Although this blog has been about ransomware, the same steps can be applied to other types of threats in Azure.
For more information about the Azure Security Stack Mappings, check out the MITRE ATT&CK Security Stack Mappings: Azure course on the AttackIQ Academy.