Security teams today are shifting their mentality from a “siloed fortress” approach, to a holistic, threat-informed defense strategy enacted by “purple teams”—collaborative entities formed by blending red and blue tactics.
How do you improve your security posture by standing up a purple team strategy? Here are 10 important things to keep in mind from the Purple Teaming for Dummies eBook.
Dive headfirst into an organizational culture shift.
As Andy Warhol famously said, “They always say time changes things. But you actually have to change them yourself.” If there’s ever been a time to shift the way we think about our cybersecurity practices, it’s now. Embrace the opportunity! As you guide your team to a purple teaming mindset, pump up the benefits of this type of construct: more aligned processes, increased visibility into the effectiveness of your security program, and of course—most importantly—thwarting adversarial efforts with data-driven insights. And don’t forget to keep your leaders and stakeholders involved and informed on plan, progress, and payoff.
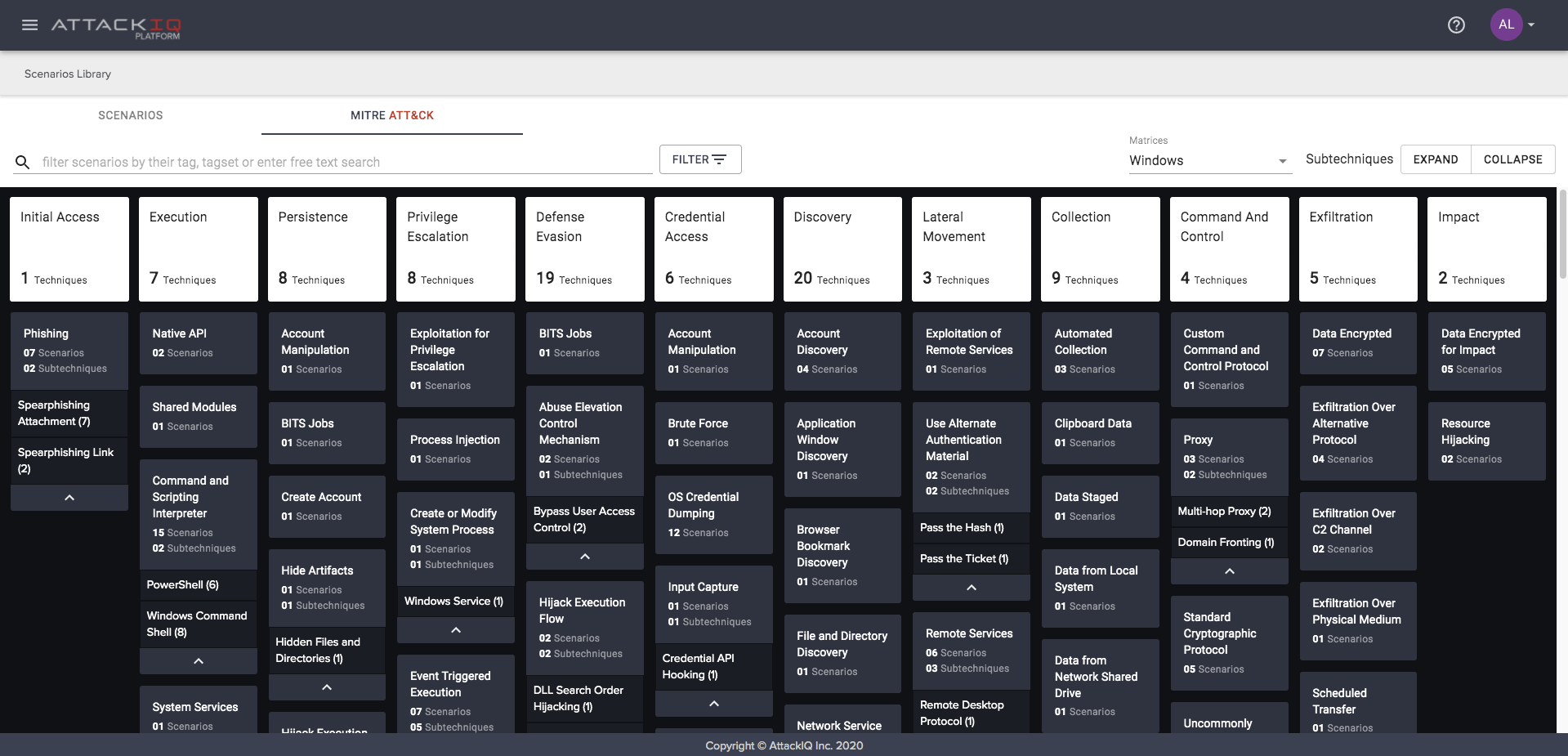
Leverage the MITRE ATT&CK framework.
The MITRE ATT&CK framework is essentially a periodic table of adversarial TTPs—tactics, techniques, and procedures—that you can use to organize your testing and strategy. This is an invaluable resource for purple teams to prioritize testing, investing, and planning as strategies evolve to meet new and existing threats. If you’re unfamiliar with how to operationalize the MITRE ATT&CK framework for your organization, you’ll get everything you need to know from the MITRE ATT&CK for Dummies eBook—a delightful companion to this one, and a popular resource amongst the community of cybersecurity professionals.
Be aware of your team’s strengths.
You need your red team to act like the adversary and predict bad actor behavior. You need your blue team to bring your organization’s unique cybersecurity capabilities and requirements to the forefront. The beauty of purple teaming is that it blends the two points of view into a more collaborative, actionable approach to tackling your readiness/resiliency plan. CISOs should facilitate this type of collaboration, encouraging teams to review attack variants and TTPs outlined in the MITRE ATT&CK framework, and then developing together a list of techniques to test against. Detailed attack descriptions live in that framework, and can guide discussions around existing threats, your company’s current controls, any gaps, and options for attack response and resolution.
Improve. Rinse. Repeat.
Security control validation is only effective if it’s continuous. And the same is true for assessing learnings from red and blue teams together. According to Purple Teaming for Dummies,
“Continuous learning is at the center of a purple team construct. Red teams learn to test blue repeatedly, at scale, to validate your organization’s defenses. Blue teams learn the thrill of elevating their cyberdefense capabilities against the adversary over time, and see the benefit of continuous testing as they run emulations in partnership with the red team, reveal gaps in defenses, and improve their defense performance.”
This idea of continuous learning is key to the purple teaming concept, and benefits your organization on an ongoing basis.
Identify and test defense assets that matter most.
Here again, collaboration is key. The blue team is responsible to protect your organizations assets, but without the red team’s input on how those can be compromised, there’s a black hole in strategic planning. What “crown jewel” assets will adversaries seek to target and obtain? How easily can they do it? What do you need to do to protect those assets? Give your red and blue teams the opportunity to share both of their perspectives for a holistic approach to cybersecurity effectiveness.
Have a strategy for 24/7 testing.
It’s become increasingly apparent that “one-off” testing isn’t sufficient to run an effective cybersecurity practice. Once you’ve identified your most important assets to protect, test controls continuously and use performance data to validate success. By combining the MITRE ATT&CK framework, security testing and optimization, and purple teaming, security teams can “de-risk” with a threat-informed defense.
Test people, processes, AND tech.
What would happen if you find a security control has failed? Purple teaming can help you understand failures that should be detected and prevented, any misconfigurations you need to address, or other problems (with personnel or process, for instance) that could have contributed to–or caused—the issue. (Chapter 4 of the Purple Teaming for Dummies eBook digs into an interesting healthcare case study around this exact issue.)
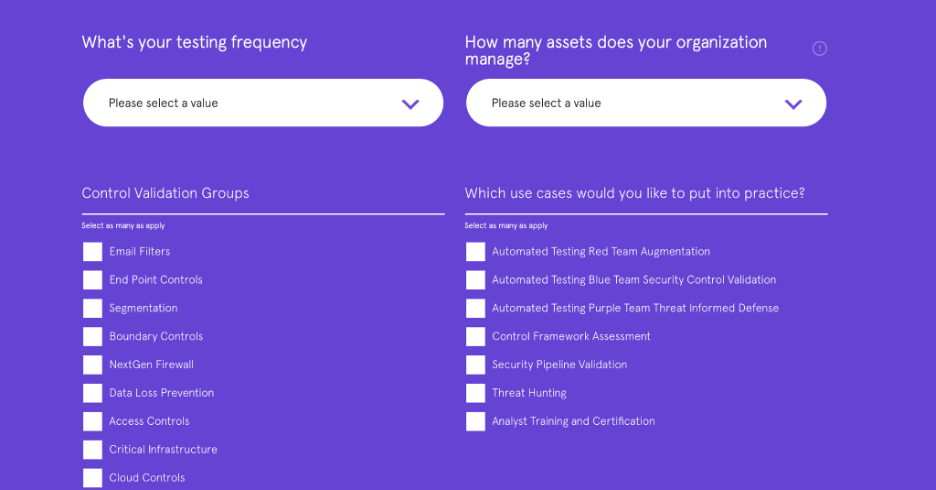
Augment with automation—and here’s a way to get started easily.
“Manual” has become a dirty word — from automobile transmissions to cybersecurity testing. No matter the size of your security team, you can leverage automation in your environment (alongside the MITRE ATT&CK framework) to augment the work your red team is doing. By automating testing, you can save money, improve your cybersecurity posture, and increase the productivity of your team. And you don’t have to go into the process blind— try this free automation transformation calculator. By answering a few simple questions around your testing frequency, assets your organization manages, control validation groups, and use cases you’d like to put into practice, you can get a personalized report with next steps unique to your organization.
Set up a strong line of communication.
This point is one that goes without saying, really, and is the essence of purple teaming. The more your red and blue teams communicate, the stronger your security strategy will be. Additionally, the better you can communicate to company leadership and the board, the more your program will flourish. Ensure your management team and the board understand the purple teaming construct and rationale behind it, goals, and outcomes, as they emerge. Be sure you can answer questions around if a certain attack can happen to you, how to de-risk, and should an attack occur, your resiliency plan for continuing operations.
Centralize performance data.
Purple teaming ensures that teams are huddling on preparing for threats that could affect them the most, and that they have visibility into cybersecurity program effectiveness. A leader that can manage a threat-informed defense strategy will help you transition into a data-driven, management-focused strategy that encourages reliance on metrics, effectiveness, and collaboration so you can be as certain as possible that your program and controls are working the way they should to keep the bad guys out.
This is just a peek at the roadmap for purple teaming. For a full crash course with tips to help you get started, download the Purple Teaming for Dummies eBook.






