CTEM Implementation service
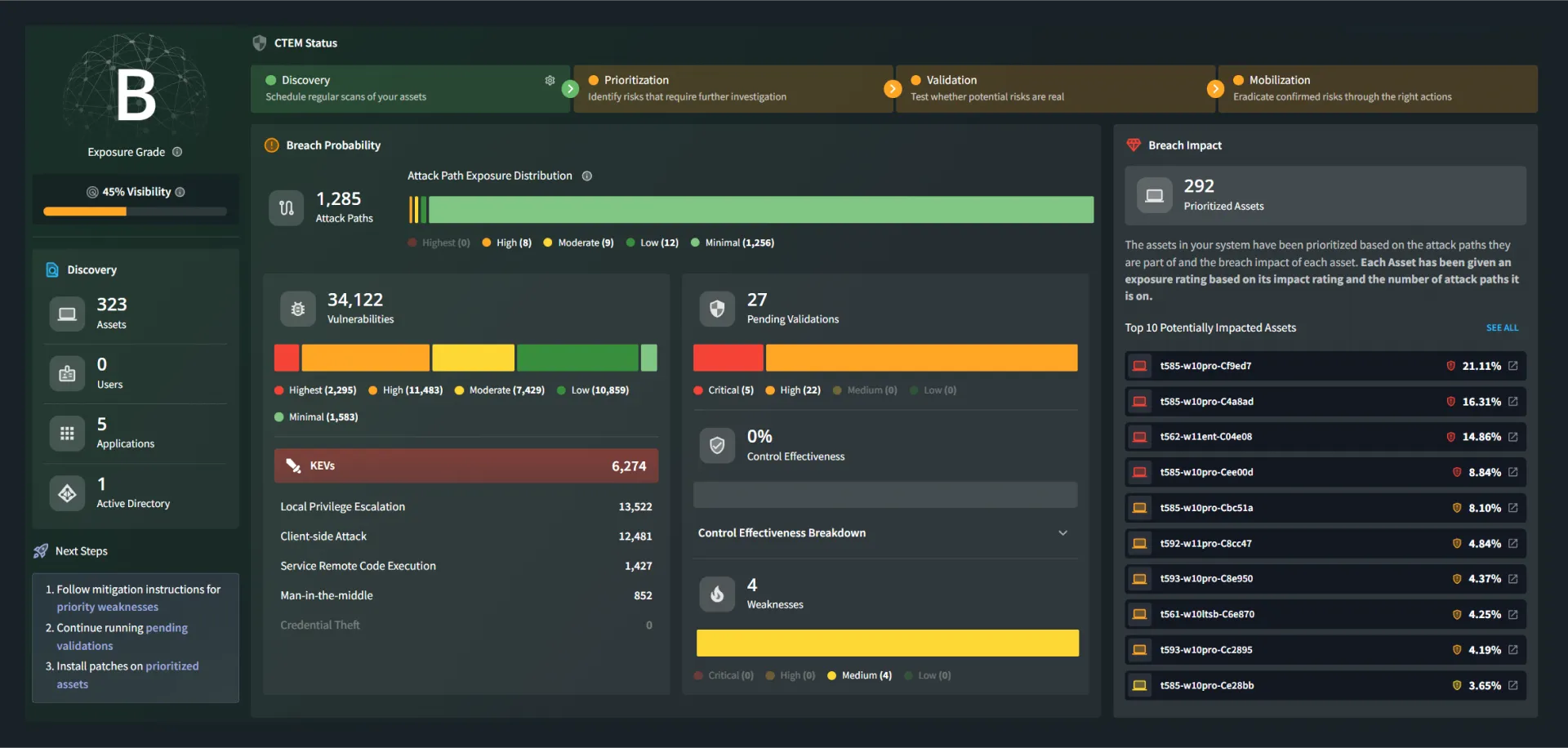
Optimize Your CTEM Program with Measurable Outcomes
Get your Continuous Threat Exposure Management (CTEM) program operational with clear metrics, a defined model, and expert guidance.
What This Service Delivers
Unified CTEM Framework
Apply CTEM principles, maturity guidance, and threat-informed practices consistently across the organization.
Cross-Functional Alignment
Establish clear ownership and collaboration across security, IT, and risk teams.
Baseline Operating Model and Metrics
Define performance indicators that enable tracking, prioritization, and decision-making.
Maturity Roadmap and Action Plan
Develop a structured, prioritized improvement plan to advance program capability over time.
How the Engagement Works
Train
Build the Foundation
A focused workshop introduces the program structure and foundational concepts.
Organize
Define Operating Model
Working sessions to design the operating approach for day-to-day execution.
Optimize
Drive Measurable Outcomes
Ongoing advisory support helps teams measure effectiveness and refine execution.
What You’ll Walk Away With
A shared understanding of how exposure management is applied
Clearly defined ownership and operating expectations
Performance indicators to support decision-making
A prioritized roadmap for continued improvement
AttackIQ advisors provide hands-on guidance throughout the engagement to support ongoing program maturity.
Why AttackIQ
AttackIQ helps organizations reduce risk by validating security controls against real-world adversary behavior. Its CTEM-aligned platform enables a structured, risk-based approach to identifying, prioritizing, and addressing exposures.
As a founding Research Partner of MITRE’s Center for Threat-Informed Defense, AttackIQ brings deep expertise in applying threat-informed practices to operational programs. AttackIQ Professional Services advisors draw on experience across government, intelligence, and commercial environments to help organizations turn strategy into measurable outcomes.
Ready to
get started?
Build a measurable CTEM program and take the next step toward reducing risk.