The AI Vulnerability Storm
How AI is changing exploitation and what security teams must do next.
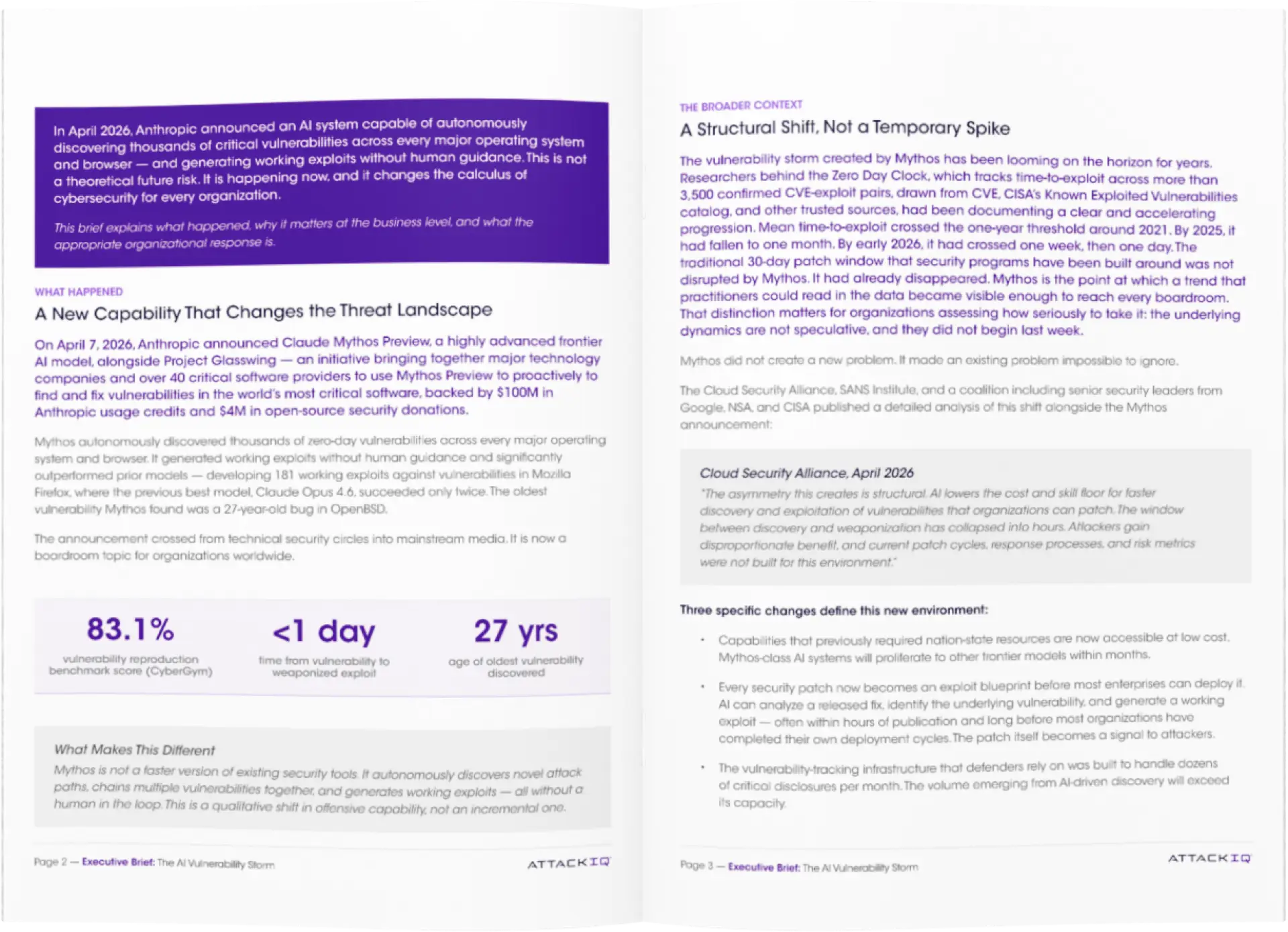
AI is collapsing the time between vulnerability discovery and exploitation. In some cases, it now takes less than a day to move from CVE to working exploit.
Most security programs were not designed for that reality. They prioritize vulnerabilities by severity and focus on patch velocity. Attackers operate differently. They chain weaknesses together and move along attack paths that lead to critical systems and data.
That’s the gap. You can reduce vulnerability counts and still increase exposure.
The question is no longer how many vulnerabilities exist. It’s which ones are actually exploitable in your environment and contribute to real attack paths.
Leading teams are shifting their approach. They focus on exposure, validate defenses against real techniques, and continuously test whether controls hold up under attack.
Get the full executive brief to understand what has changed and how to adapt your program.
Read the Research →
Download the White Paper
By submitting this form you indicate that you have read and agree to the terms of our Privacy Policy.
