AttackIQ Enterprise
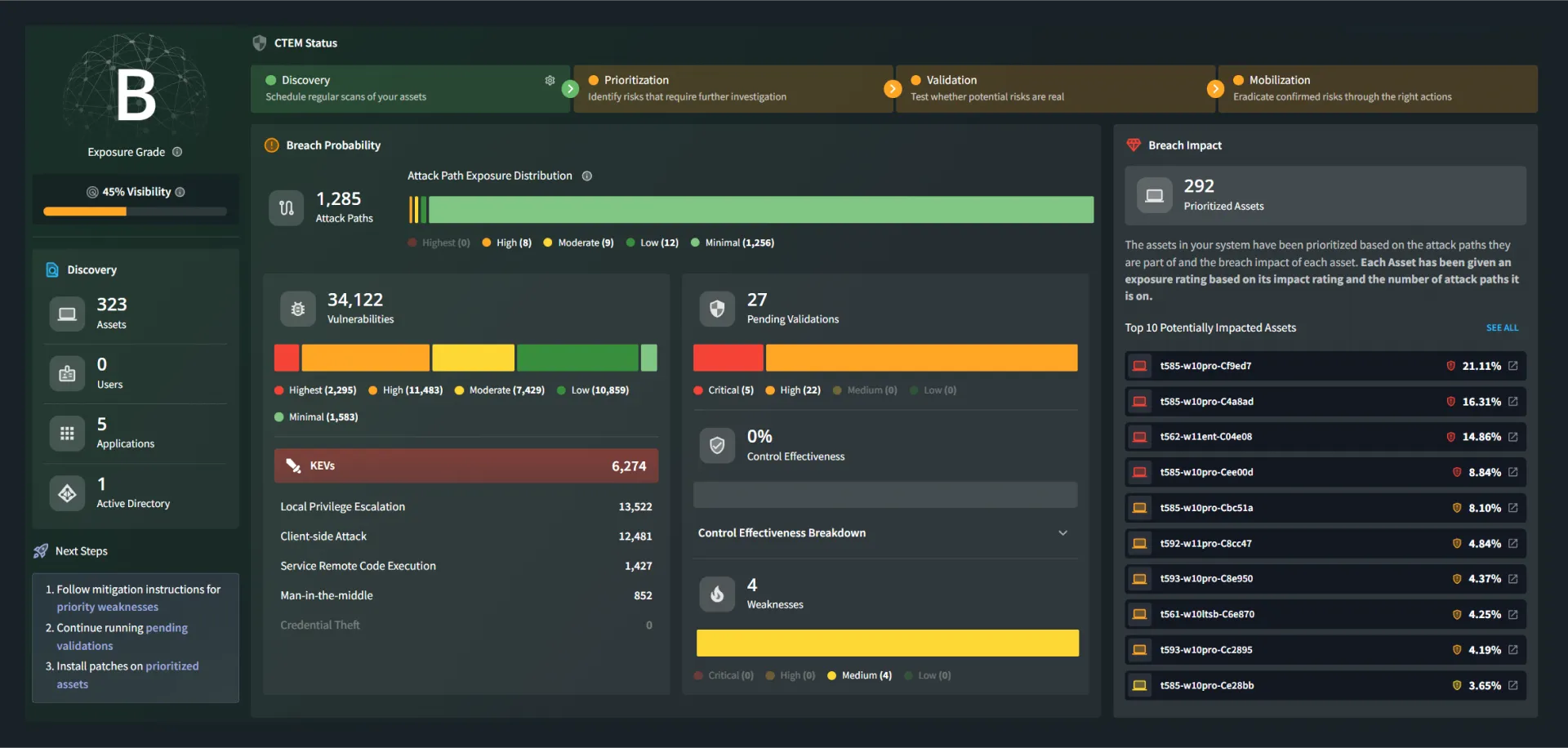
Advanced Exposure Management at Scale
Exposure Validation That Works Like Your Organization
From custom threat simulations to global test orchestration, Enterprise gives you the tools to continuously assess, adapt, and advance your security program.
Design Custom Adversary Scenarios
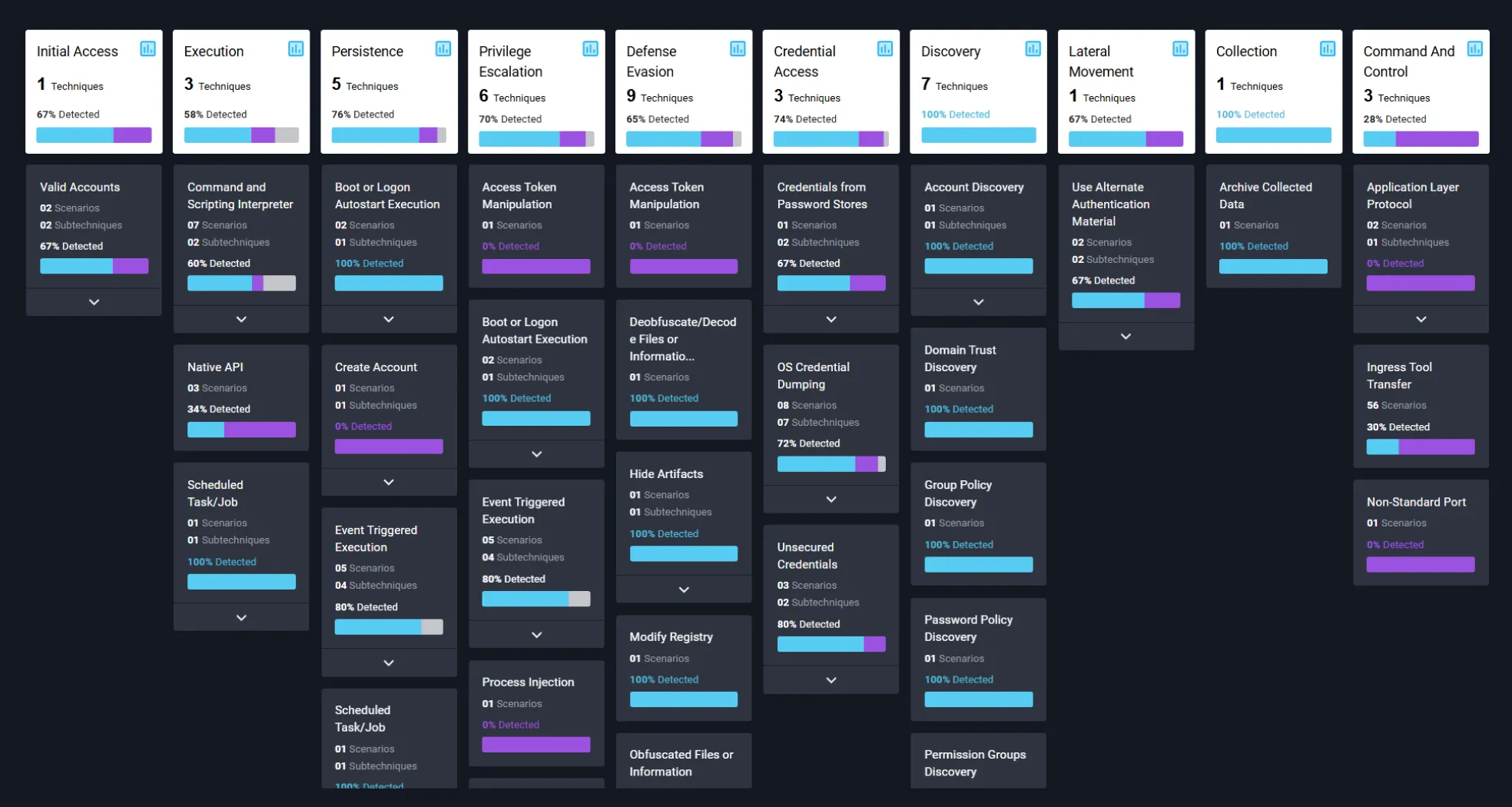
Build and run advanced, multi-stage attack simulations tailored to your infrastructure—testing lateral movement, persistence, and exfiltration across complex environments.
Orchestrate Enterprise-Wide Validation
Coordinate testing across teams, business units, and hybrid environments with centralized governance, role-based access, and framework-aligned reporting.
Translate Testing into Strategy
Turn technical validation data into board-ready insights that demonstrate control effectiveness, quantify risk reduction, and support informed security decisions.
Embed Continuous Readiness
Integrate persistent validation into daily workflows with reusable test plans that evolve with your infrastructure and promote a culture of measurable improvement.

Your Program, Your Playbook, Your Results
Streamline security operations with tailored testing, scalable automation, and actionable reporting aligned to business risk and CISO priorities.
Fast Time to Value
Gain immediate visibility into your security posture with baseline assessments and seamless onboarding. No complex deployment required.
Flexible, Actionable Reporting
Generate on-demand reports tailored to security leaders, boards, auditors, and cyber insurers. Track remediation progress, control performance, and exposure trends.
Targeted Remediation Guidance
Receive prioritized, easy-to-execute recommendations based on testing results. Confirm improvements through automated retesting.
Continuous, Real-World Testing
Automate MITRE ATT&CK–aligned emulations across your stack, targeting the threats and attack paths most relevant to your organization.
Cyber Insurance Support
Demonstrate control effectiveness and reduce premiums with audit-ready reporting built to satisfy insurers and regulators.
Boundary Control validation
Continuously assess perimeter defenses to identify misconfigurations, drift, and exploitable exposures across hybrid environments.
Intelligence from the Adversary Research Team
un updated adversary emulations, attack graphs, and PCAP-enabled scenarios—developed in response to emerging threats and public advisories.
Expert Consulting and Strategic Support
Access AttackIQ’s security consultants to design your testing program, align to CTEM, and interpret results in the context of business risk.
Security Training Readiness You Can Measure
Track your team’s training progress with real-time visibility into course completions, exam scores, and readiness metrics—ensuring your analysts are as prepared as your technology.
AttackIQ Mission Control

Up-Level Your Teams
Role-based insights and dedicated workspaces lower the bar for less skilled users to conduct testing.
Actionable Data
Reviewers gain valuable insights from comprehensive analytics to guide ongoing security improvements.
Simplified Administration
Ensure mission alignment by enabling managers to create and assign testing objectives to team members easily.
Improved Efficiency
Streamlined workflows empower users to swiftly address and focus on their assigned security issues, leading to better ROI.
Your Co-Pilot for Continuous Readiness
Simulate real-world attacks, validate your defenses, and reduce risk with expert-driven testing. Stay proactive and resilient—contact us to get started.
FAQs
Never Settle for Uncertainty
Validate Your Defenses
Take the guesswork out of threat exposure management. Validate your defenses with real-world attack scenarios and focus on what matters most—managing your risk.