The Pyramid of Pain Explained: Validate What Hurts Attackers Most
Disrupt adversary operations by targeting their most valuable techniques and validating your defenses using CTEM and AEV.
What is the Pyramid of Pain?
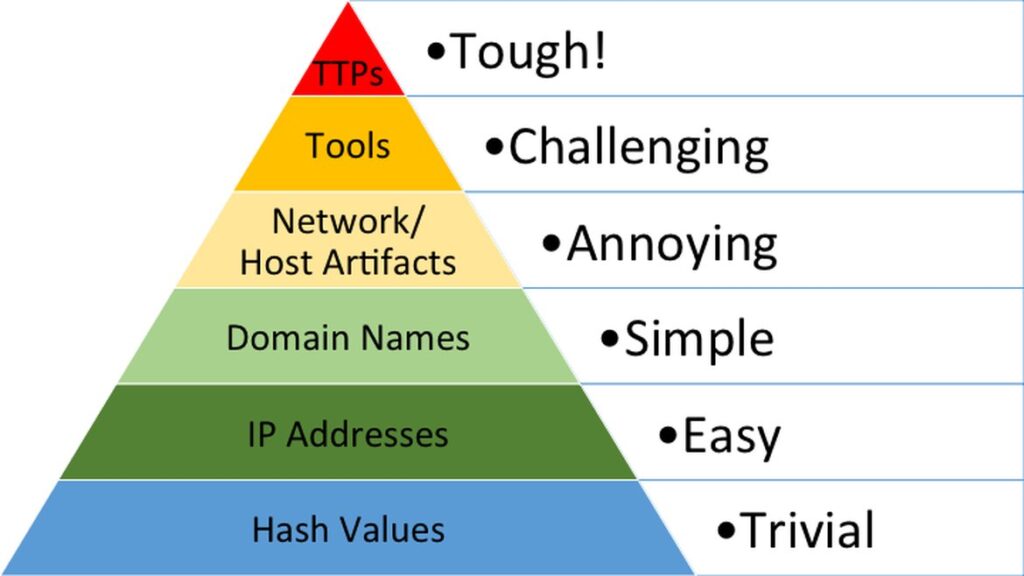
The Pyramid of Pain, created by security professional David J. Bianco in 2013, is a foundational model for understanding the effectiveness of cybersecurity controls. It shows that while some indicators of compromise (IOCs) are easy for attackers to bypass, others, like behavioral tactics, are far more disruptive when denied.
The Pyramid of Pain Framework at a Glance
The Pyramid of Pain consists of seven levels, from easiest to hardest for attackers to change:
Today, this model plays a critical role in threat-informed defense, especially as organizations adopt Continuous Threat Exposure Management (CTEM) and leverage Adversarial Exposure Validation (AEV) to validate exposures. By targeting the right indicators, security teams can disrupt adversary operations and prove security control effectiveness at every level.
Why It Matters for CTEM and AEV
| Indicator Type | Strategic Impact | How to Validate with AEV |
|---|---|---|
| Hash values | Provides minimal long-term value as attackers can easily recompile malware to change hashes | Deploy known malicious files to validate antivirus (AV) and endpoint detection and response (EDR) capabilities. |
| IP addresses | Creates temporary disruption but requires constant updating as attackers rotate infrastructure | Simulate connections to malicious IPs to test firewall and intrusion prevention system (IPS) rules. |
| Domain names | More disruptive than IPs; forces adversaries to register new domains and update their malware | Test web proxies and DNS filtering via malicious domains. |
| Network artifacts | Requires attackers to modify their communication methods and command-and-control protocols | Emulate suspicious traffic patterns and command-and-control protocols. |
| Host artifacts | Significantly raises costs by forcing attackers to modify their footprint on target systems | Create benign files mimicking malware behaviors for EDR validation. |
| Tools | When blocked, requires adversaries to invest in developing or acquiring custom tooling | Use common attacker tools in a lab to validate alerting and control. |
| TTPs | Highest-value target that forces complete attack retooling when detected and blocked | Run full attack chains mapped to MITRE ATT&CK to test holistic security posture. |
How Does the Pyramid of Pain Work?
The pyramid helps network defenders and security operations center (SOC) teams understand where to focus their detection and prevention efforts. Lower-level indicators like hashes and IP addresses are easy for adversaries to change, offering minimal disruption. Higher up, indicators like TTPs are harder to modify, so targeting them imposes greater operational cost on attackers.
For example:
Similarly, if a defender’s network security controls use IP address, CIDR block, or even ASN range blacklists to disrupt malicious network communication, the Pyramid suggests they may still be in trouble as these controls are “easy” to circumvent (in this case, the attacker could simply move their command-and-control infrastructure or operations center to another network server).
Why It Matters for CTEM and AEV
Nearly all IOCs are transitory—they lose value over time. The exception is attacker behavior. Focusing on behavioral indicators—TTPs—forces adversaries to change how they operate, not just what they use.
This aligns directly with threat-informed defense practices and frameworks like MITRE ATT&CK. It also reinforces the strategic value of validating controls against attacker behavior, not just static IOCs.
Pyramid of Pain FAQ
BAS vs AEV — From Simulation to Real-World Readiness
While Breach and Attack Simulation (BAS) tools simulate specific attack scenarios, AEV delivers continuous, real-world validation using actual adversary behavior. The Pyramid of Pain shows why this matters—validating behaviors, not just artifacts, drives true operational resilience.
Ready to Operationalize the Pyramid of Pain?
See how AttackIQ helps security teams validate defenses against real-world adversaries—continuously and safely.
Explore the AEV platform