A recent report published by SonicWall indicates that ransomware has increased by 151% in the first half of 2021, compared with the same time period in 2020. With a reported 304.7 million attempted ransomware attacks, and some of the major attacks reported so far in 2021, it’s clear that there are no signs of ransomware slowing down any time soon.
Although ransomware can have devastating effects regardless of which industry vertical an organisation is part of, the healthcare industry has particularly paid a heavy price in recent times. To understand the risks associated with cyberattacks targeting the healthcare industry, let’s start by taking a look at some past and present examples. While there are too many to list, some of the more landmark attacks are listed below.
Healthcare Attacks:
Anthem (2015)
Anthem disclosed a breach back in February 2015 which saw almost 80 million medical records leaked. The attack started with a successful phishing email attachment being opened, which led to the attackers moving laterally and gaining access to numerous accounts and systems. The Anthem attack was later attributed to the advanced threat actor known as Deep Panda.
UK National Health Service (NHS) (2017)
WannaCry resulted in 81 of 236 NHS trusts becoming impacted by the infamous ransomware attack. Of the 81 trusts impacted, none of them were found to contain the critical Microsoft patch released a few weeks prior, which led to successful infection via the EternalBlue vulnerability.
SingHealth (2018)
A chinese espionage group known as WhiteFly successfully managed to steal 1.5 million patient records, of which 159,000 of those were outpatient records back in June/July 2018. One of the contributing factors from the report highlighted that despite a cloud migration being almost complete at the time of the incident, an open network connection was left open, allowing attackers to query the database storing the medical records.
Düsseldorf University Hospital (2020)
A ransomware attack led to the closing of the accident and emergency department at the Düsseldorf University Hospital, Germany. While initial reports suggested that this resulted in the death of a patient due to being rerouted to an alternative hospital 32 KM away, the investigation that followed concluded that the delay was of no relevance to the final outcome. This still serves as a stark reminder of the potential impact that ransomware could lead to in the physical world.
UVM Health (2020)
A successful ransomware attack led to incurring costs of upwards of $63 million. While the details of the group are not yet known, the infrastructure had to be completely rebuilt before restoring from backups.
Health Service Executive (2021)
The publicly funded healthcare service in the Republic of Ireland fell victim to Wizard Spider, an advanced Russian threat group, who eventually detonated Conti ransomware onto systems and demanded a ransom of $20 million. Ireland’s Department of Health narrowly avoided becoming a victim from this same attack by shutting down it’s infrastructure as a precaution.
Scripps Health (2021)
A healthcare provider in San Diego fell victim to a recent ransomware attack that occurred in May. The investigation is still ongoing but another one to watch.
Grupo Fleury (2021)
The Brazilian healthcare company was recently hit by a cyber attack in June of this year. Although not publicly confirmed, it is thought that a shared ransomware sample attributes the attack to the REvil ransomware group. The investigation is still ongoing, but expect more details to come to light in the near future.
Risks to Healthcare
Beyond the financial costs to a healthcare organization, here are some of the unique risks posed to the healthcare sector.
- Stolen/leaked patient medical records
- Encrypted patient records or other data critical to the running of a healthcare organisation
- Selling of leaked data on dark web marketplaces which could result in future fraudulent activities including identity theft
- Damage or loss of service to critical medical devices or other critical systems
- Closure of departments and entire hospitals
- Delay or cancellation of critical primary care and treatment
- Delay or cancellation of secondary care (e.g. obtaining medical results)
- Delay in returning services and equipment to BAU
Lessons Learned from Past Healthcare Cyberattacks
While we can only speculate about some of the details regarding recent cyberattacks in the healthcare sector, we can be sure that these attacks were successful due to some breakdown in the three aspects of a security control: people, processes and technology. Listed below are some specific recommendations that healthcare providers should consider as a priority.
Defense in Depth
Using a defense in depth approach for technical and non-technical controls. Purple Teaming plays an important part here.
Cyberdefense Capability Review
Teams need to conduct regular, ongoing reviews of the technical and non-technical aspects of their security controls. Continuous security validation can help with continually.
Security Awareness Training
Ongoing security awareness training, and creating a vigilant work force will likely reduce some attack vectors such as social engineering and phishing.
Regular Security Checks
Critical systems, databases and networks must be regularly tested and validated. Improving the cyber hygiene level throughout the organisation should be seen as a continuous process. Threat hunting, detection and threat emulation also plays into this.
Incident Response Processes
The incident response procedures and processes should be tested frequently.
What Next?
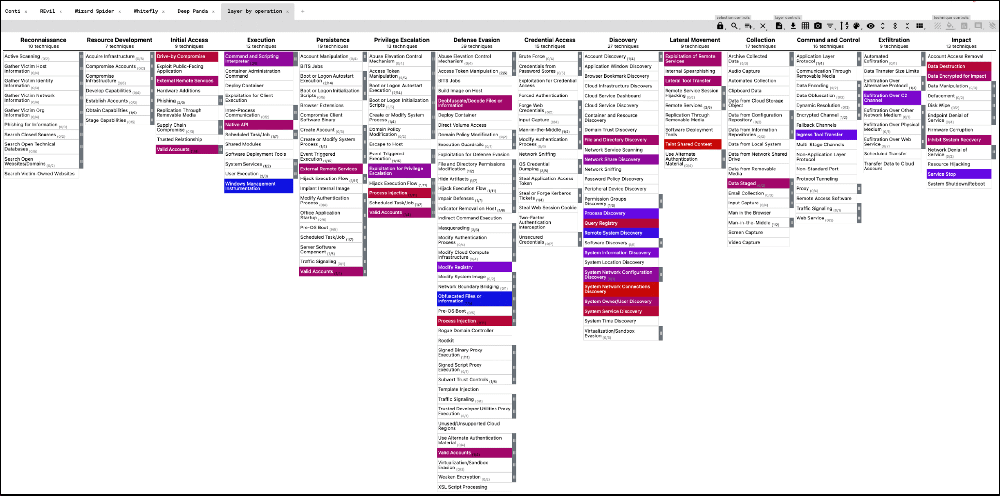
If you have an in-house cyber threat intelligence (CTI) team, or use a combination of OSINT and commercial TI tools, you may already have some idea of what threats and groups may already be targeting your organisation or sector. If not, the MITRE ATT&CK framework contains references to some of the groups and software targeting the healthcare industry. These can be loaded into the MITRE ATT&CK Navigator and added as layers.
Shown below is an example of the tactics, techniques, and procedures (TTPs) used by Conti, REvil, Wizard Spider, Whitefly and Deep Panda. Of the five groups, there are a total of 31 techniques across 12 tactics (not including sub-techniques). Of course you can tailor this to individual groups or software of interest to you. Focusing on the groups, software, and TTPs that are more prevalent in the healthcare industry can help you understand your defenses and the capabilities that matter most to you. Exporting ATT&CK Navigator leads to a JSON file which you can then import into AttackIQ, giving you a whole host of scenarios specific to each tactic and technique.