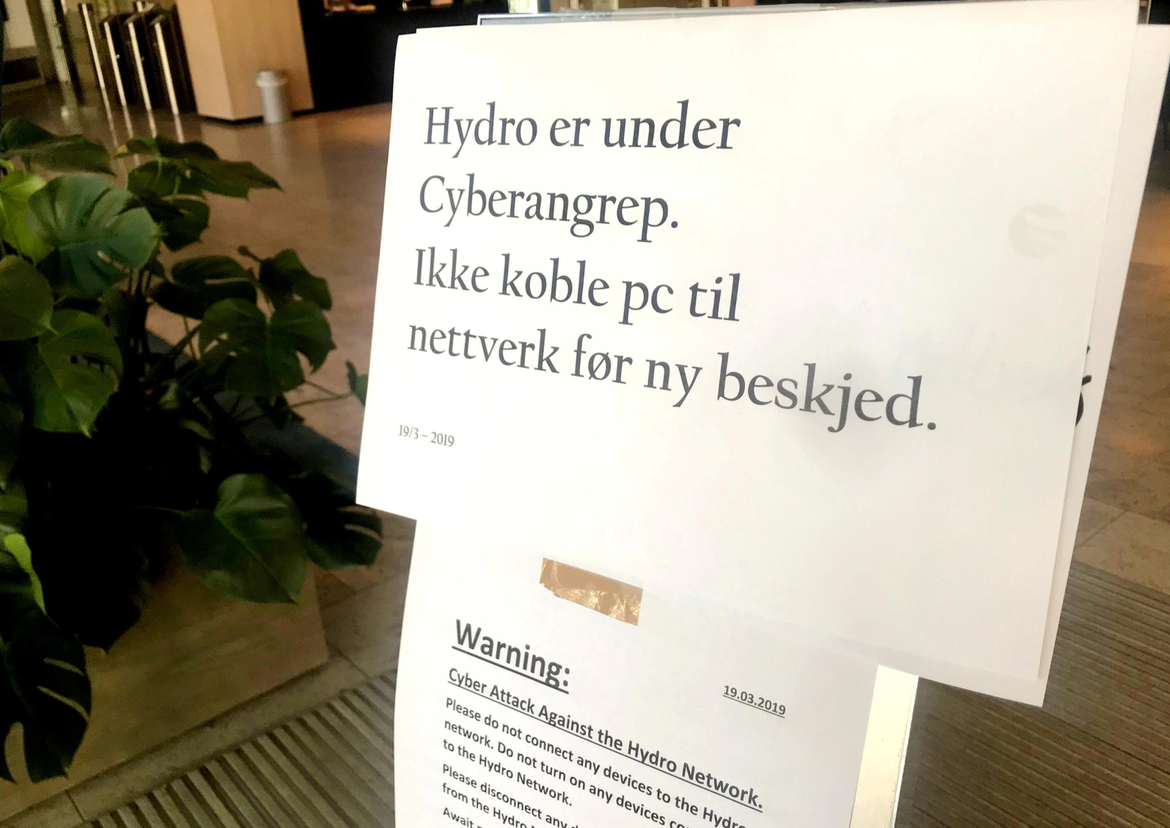
Below is a picture of a sign posted at the company’s entrance after the attack was discovered, warning employees not to connect their laptops or other devices to the company network. After the attack, their production dropped to a crawl. This has already cost the company more than $40 million in damages. On April 12, 2019, Norsk Hydro announced that it will postpone its first-quarter earnings by five weeks.
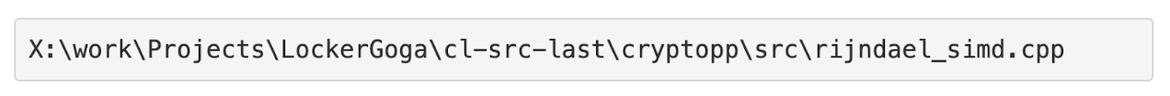
The earliest public disclosure of this strain of ransomware occurred on January 24, 2019, when Altran Technologies, a global Industrial and Engineering Consulting firm, had to shut down their network and applications due to a malware attack. The threat research community, spearheaded by the MalwareHunterTeam, quickly identified the malware and named it LockerGoga. The name is derived from the pathname of a file used to compile the source code of the malware. The file is thought to have originated in Romania, where Goga is a common last name.
The LockerGoga ransomware is not particularly sophisticated and makes no attempt to evade detection. It encrypts files with a strong symmetric key and a block cipher (AES 256) and appends a .locked extension to the encrypted versions. It encrypts files individually, and after each file is completed, it spawns a new process to carry out the next encryption. This is inefficient, as it consumes a lot of overhead and also results in slow operation.
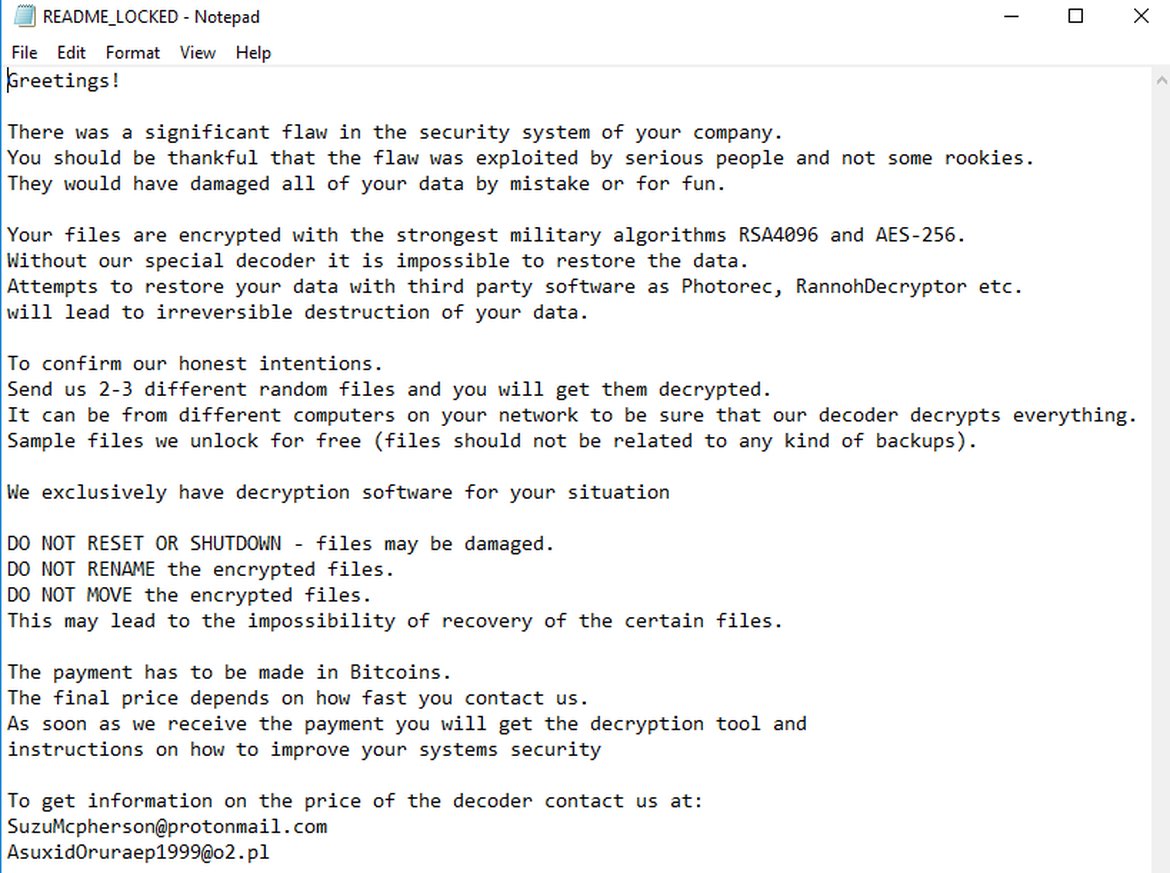
It is still not clear how the attackers gained initial access to the victims’ systems. It could be they got an unsuspecting user to click on a phishing link, or they may have bought credentials on the dark web. Once they are in, they make use of common hacking tools like Metasploit or Cobalt Strike to launch their attacks. They use credential dumping tools like Mimikatz to discover passwords in memory, where they are hunting for the domain admin credentials. Once they obtain these credentials, they use Microsoft’s Active Directory management tools to propagate their ransomware on other machines. To escape detection, they sign their code with a stolen certificate that makes their malware look like a legitimate executable and thus remain undetected. On their target machines, they also execute a “task kill” to stop the antivirus agent running there, further eliminating the possibility of detection. Once they are done with encrypting all the files, they drop a ransom note as shown below. In plain English they describe what they have done, offer to decrypt a few sample files, and ask for payment in Bitcoin, throwing in a possible discount if they are contacted quickly.
More recent versions of LockerGoga have incorporated a bizarre twist. After they are done with the file encryption, the attackers detect all the network interfaces and disable them. Additionally, they change the user and admin passwords of the computer and log off the machine. The net result is that the victim cannot even log in to their system to see the ransom note, thereby delaying their ability to contact the attacker and pay the ransom. This creates a lot more chaos and has given rise to the speculation that the attackers may not merely be looking for a profit, but could also be sponsored by nation states engaged in cyber warfare.
As of March 21, Windows Defender did not detect LockerGoga. They may have subsequently updated their signatures to detect this malware. However, if the antivirus agent is killed or if the attackers create a variant of LockerGoga with a different signature, they will continue to go undetected by anti-malware software. The more effective way to guard against these attacks is to look for unusual behavior patterns that identify malicious behavior. Many of the leading EDR vendors are adding behavioral heuristics to their arsenal so that they are able to detect ransomware attacks based on anomalous system behavior. Here are some of the characteristics of ransomware that a behavioral algorithm can look for:
Credential dumping
Most EDR vendors today detect execution of credential dumping tools like Mimikatz. There are several different variants and the AttackIQ platform has a dozen scenarios that can emulate and run many of these tools so you can evaluate your security controls for effectiveness in this area of detection.
Lateral movement
Ideally, you want to design your enterprise to minimize the ability of a user or process to move laterally through the organization. Malware typically gets into an enterprise by luring an unsuspecting user to click on an attachment or link. After the attacker has gotten in, an enterprise is best served if it can prevent an attacker from taking credentials harvested from one system and using them to access files across the network. The AttackIQ platform has ten different lateral movement scenarios that can test the effectiveness of the controls preventing a malicious process from moving to other systems in the organization.
Suspicious process activity
The LockerGoga malware spawns a number of processes, one per file that is being encrypted. This is not the expected operation of a typical end-user system. Modern security solutions are designed to incorporate behavioral heuristics and are likely to detect this pattern as abnormal. We need to develop a scenario that can mimic this type of activity so that our customers can validate if their security controls are detecting this behavior.
Large number of encryption processes
There are many variants of ransomware that encrypt files on an end system. Again, behavioral heuristics should be able to detect unusual encryption activity on an end user’s system and alert the security operator. It may be useful for us to develop a scenario that mimics the encryption activity of ransomware, so we can help our customers evaluate their controls and figure out how they would respond to such an attack.
Deletion of backup files & system event logs
To inflict maximum damage, ransomware typically deletes backup files as well as system event logs. Many EDR vendors like CrowdStrike will detect a rogue process attempting to delete backup files and stop the process. Some variants of LockerGoga are found to delete the Windows event logs after completion of the file encryption tasks. AttackIQ platform does include a scenario that emulates the “Clear Command History” TTP from Mitre ATT&CK. We might also need to create a scenario for suspicious deletion of backup files and Windows event logs.
That’s all I have for this week. Happy Hunting!